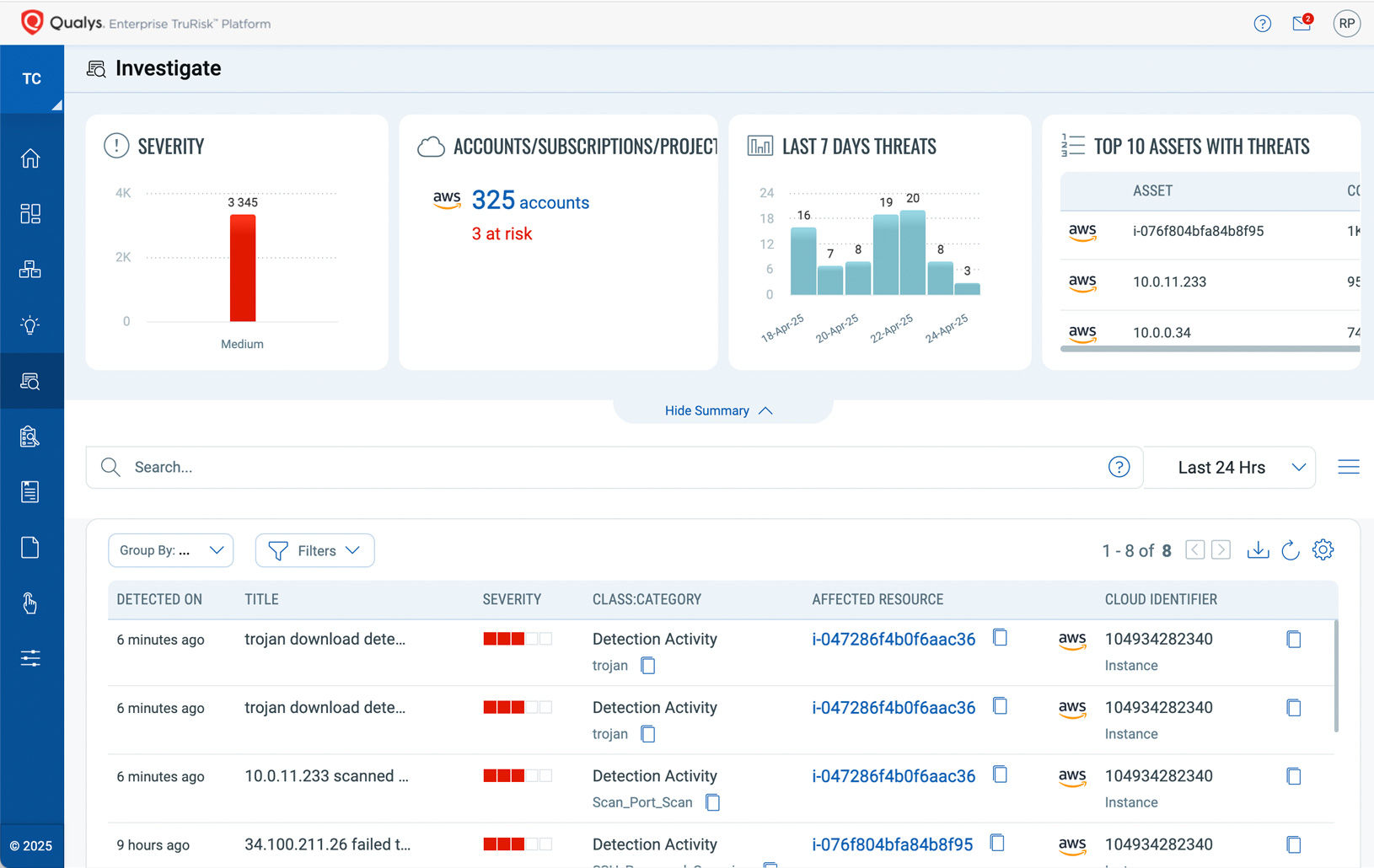
Cloud Detection and Response (CDR)
Your Cloud. De-risked.
Our CDR tool helps you detect known and unknown threats in real time with deep learning AI.
De-risk your cloud with CDR – an integral part of Qualys TotalCloud™ – an AI-powered CNAPP solution
Detect Active Exploitation
Get continuous real-time protection of your multi-cloud environment against active exploitation, malware, and unknown threats.

Detect threats from build to runtime
Detect attacks at various points along the cloud kill chain and zero-day threats. Detect known and unknown threats and identify assets that are being actively probed and protect them.

Detect zero-day and novel threats
Threats are detected in near-real-time using deep-learning AI. Unlike legacy signature-based approaches, Qualys CDR’s AI-based approach can detect zero-day and new threats from a myriad of data points.

Detect active exploitation and mitigate runtime risks
Inspect cloud network traffic for suspicious communications, unauthorized activity, crypto miners, malware, and C2 communications using deep-learning AI algorithms.
Identify lateral movements
Detection of unauthorized activity, such as brute-force attacks SSH and RDP, and port scans indicating lateral movement. This feature allows you to detect lateral movement in the organization when an attacker is attempting to infiltrate other virtual machines.
Detect threats at all points of the kill chain
Protect against emerging cloud-based attacks by inspecting network traffic to detect attacks at various points along the cloud kill chain.
Analyze network traffic
Analyzes network traffic to identify any patterns and behaviors associated with ransomware activity using AI technology and deep learning algorithms.
Improved risk prioritization based on runtime data
Improve your security, identify assets that are being actively probed, and automatically take the necessary action to improve security.
No signature, no rules
Leverage deep learning AI to detect unknown threats in less than a second without using legacy signature-based tools.
Explore TotalCloud CDR Product Tours
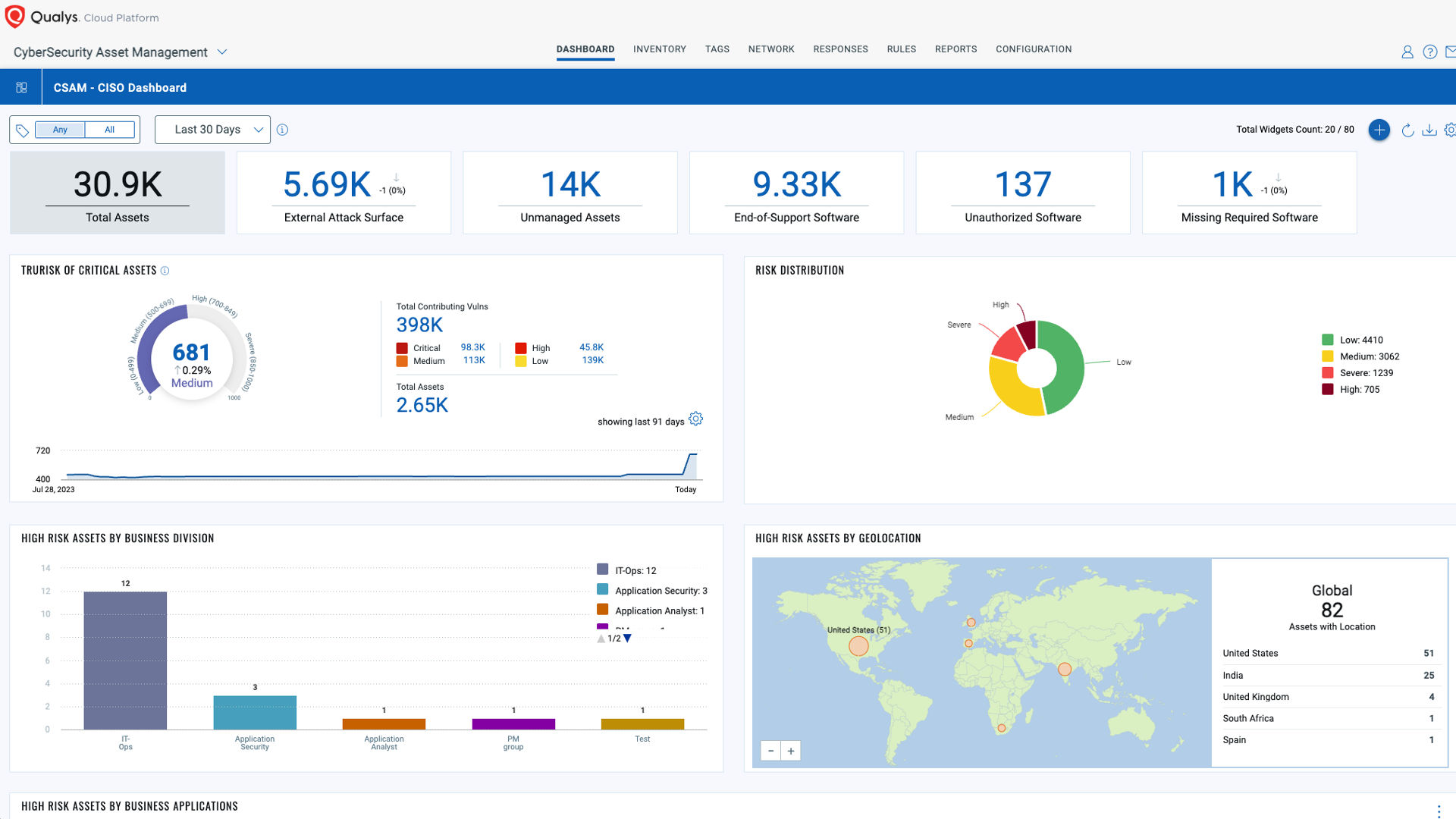
Powered by the Enterprise TruRiskTM Platform
The Enterprise TruRisk Platform provides you with a unified view of your entire cyber risk posture so you can efficiently aggregate and measure all Qualys & non-Qualys risk factors in a unified view, communicate cyber risk with context to your business, and go beyond patching to eliminate the risk that threatens the business in any area of your attack surface.