Measure Risk
with 25+ sources of Real-Time Threat Intelligence (RTI) using TruRisk™.
De-risk your security posture with real-time threat intelligence, risk prioritization, and reduced MTTR.
Measure Risk
with 25+ sources of Real-Time Threat Intelligence (RTI) using TruRisk™.
Communicate Risk
By routing vulnerabilities to the right owners, driving focus on critical business risk.
Eliminate Risk
60% faster with built-in patching and remediation workflows.
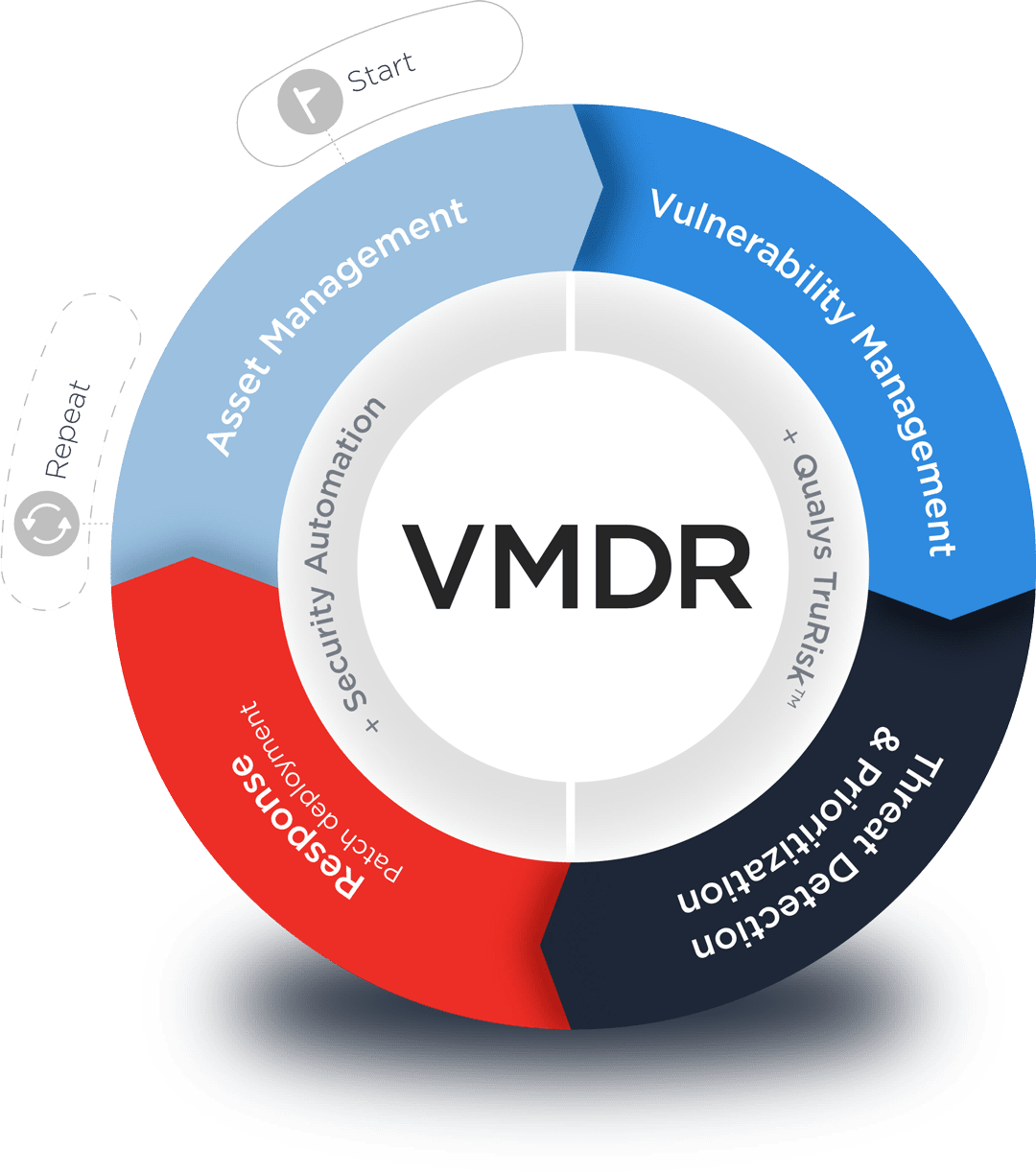
Modern vulnerability management is more than just a list of detections and CVEs. Prioritize using TruRisk™ with Real-Time Threat Intelligence and remediate within a single platform.

Risk-based vulnerability management is more than a list of detections. Ditch your legacy scanner to measure business risk in the universal language of TruRisk™ with integrated VMDR includes:
“Qualys scans it, finds it, patches it. That's it. In terms of time, manpower, planning, and the cost reduction in savings of labor dollars...huge.”

“VMDR detected ten times more vulnerabilities than in the same period the previous year.”

The Enterprise TruRisk Platform provides you with a unified view of your entire cyber risk posture so you can efficiently aggregate and measure all Qualys & non-Qualys risk factors in a unified view, communicate cyber risk with context to your business, and go beyond patching to eliminate the risk that threatens the business in any area of your attack surface.
