Protect your mid-sized business
70%
of firms have 5+ standards and frameworks
$4M
average lost revenue from one audit failure
424%
Increase in breaches due to misconfigurations in 2022
Measure, Communicate, and Eliminate Cyber Risk by Simplifying Compliance
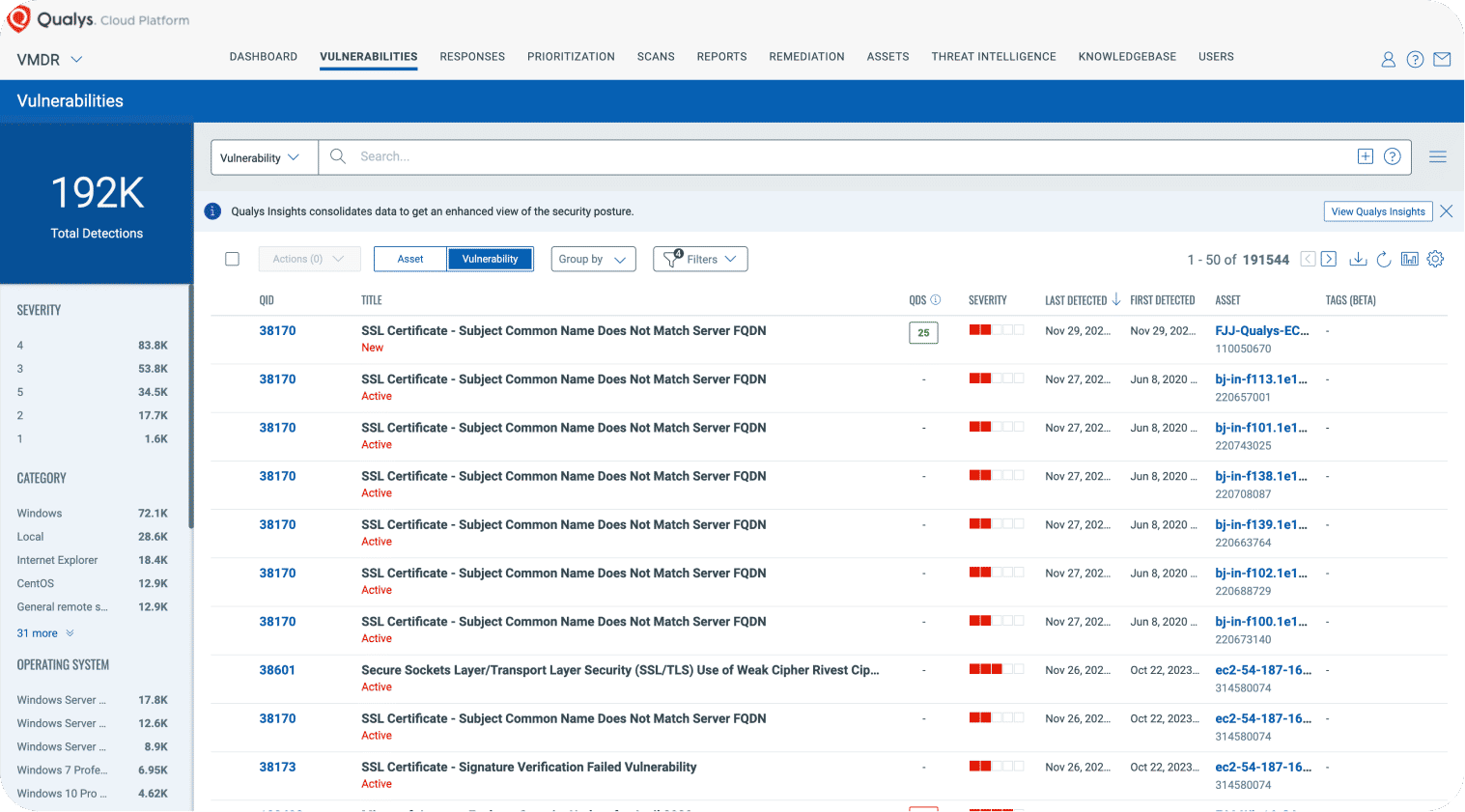
Policy Compliance DatasheetExtend Compliance Coverage from VMDR
Qualys Compliance Solutions are built natively into the Enterprise TruRisk Platform. Combined with VMDR, customers can
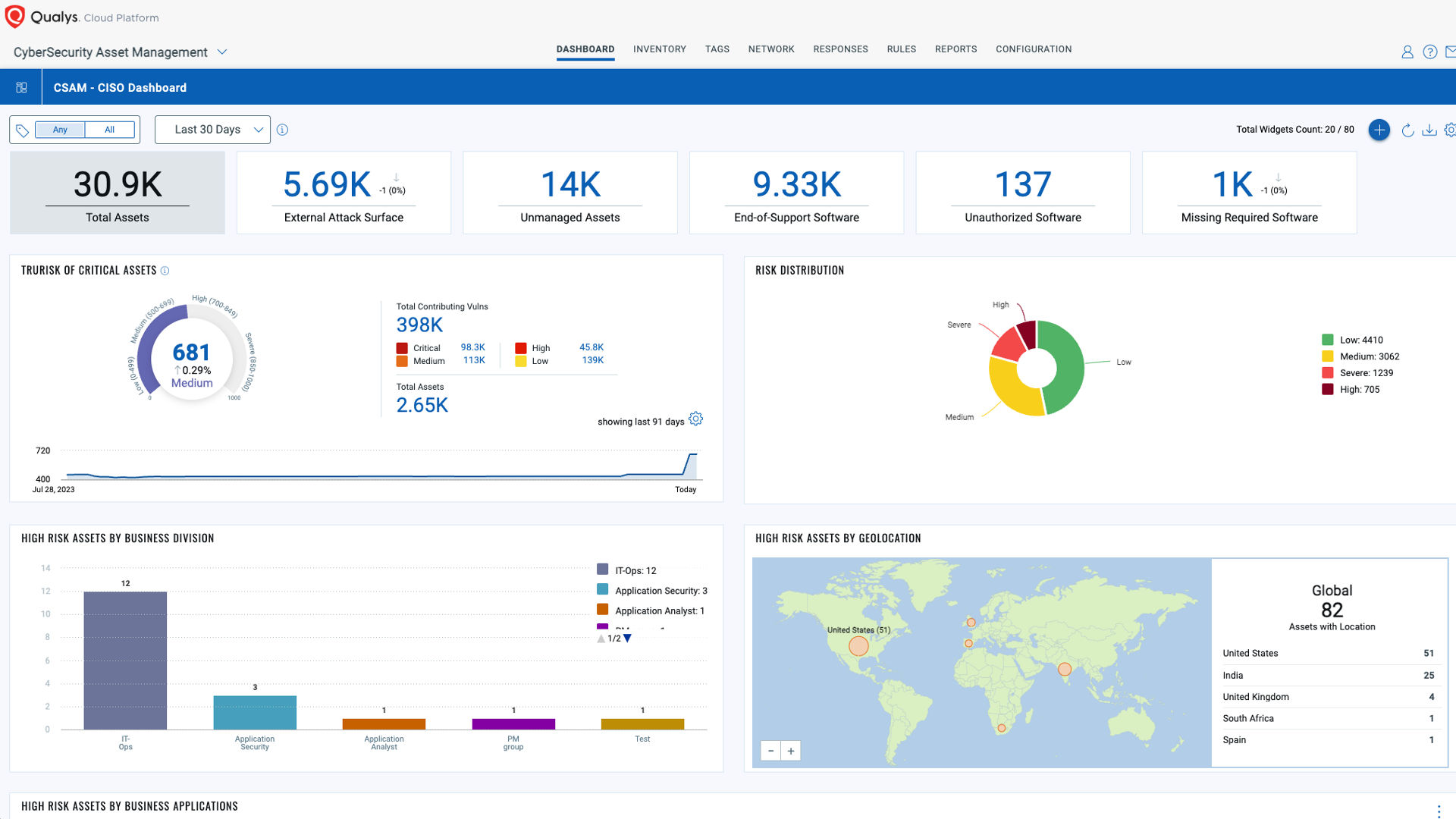
Create compliance dashboards to highlight compliance gaps and provide pre-built templates, profiles, and policies to achieve full compliance.
Measure, communicate, and eliminate cyber risk across the global hybrid IT environment.
Clearly report and articulate risk to internal and external compliance stakeholders across 950 policies, 20,000 controls, and 100 regulations.
More on VMDRDe-risk your business while reducing audit failure risks.
What’s Included in the Qualys Compliance Solutions Set?
Policy Audit (PA)
File Integrity Monitoring (FIM)
Security Assessment Questionnaire (SAQ)
Custom Assessment and Remediation (CAR)
CyberSecurity Asset Management (CSAM)
PCI Approved Scanning Vendor (ASV)
Powered by the Enterprise TruRiskTM Platform
The Enterprise TruRisk Platform provides you with a unified view of your entire cyber risk posture so you can efficiently aggregate and measure all Qualys & non-Qualys risk factors in a unified view, communicate cyber risk with context to your business, and go beyond patching to eliminate the risk that threatens the business in any area of your attack surface.





