Qualys’ offerings for AWS follow our Transparent Orchestration principle: They simplify AWS security by eliminating friction, and making it intuitive and automated. We accomplish that via Qualys’ native integration with AWS.
Public Cloud Integrations for Security and Compliance
Total visibility of your public cloud deployments.
Cloud computing platform providers operate on a “shared security responsibility” model, meaning you still must protect your workloads in the cloud. Qualys can help.
- Identify, classify, and monitor assets and vulnerabilities
- Comply with internal and external policies
- Prioritize vulnerability remediation
- Automatically find and eradicate malware infections on your websites
Security and compliance via native integrations
For Amazon Web Services (AWS)
For Microsoft Azure
 For Google Cloud Platform
For Google Cloud Platform For Oracle Cloud Infrastructure
For Oracle Cloud Infrastructure
Qualys + AWS Highlights
Complete visibility, and end-to-end IT security and compliance of your AWS deployments and hybrid IT.
Built for AWS with Transparent OrchestrationTM
2-second visibility across all workloads and PaaS resources
Qualys provides instant, full visibility into your AWS deployments, with details on how instances are being secured and what workloads and resources are running on them.
Continuous assessment of your global security and compliance posture
Qualys continuously monitors and assesses your AWS assets and resources for security issues, misconfigurations and non-standard deployments.
Identify zero-day vulnerabilities and compromised assets
With Qualys, you can continuously detect vulnerabilities, including zero-day bugs being exploited in the wild, pinpoint the AWS assets requiring immediate fixes and prioritize remediation.
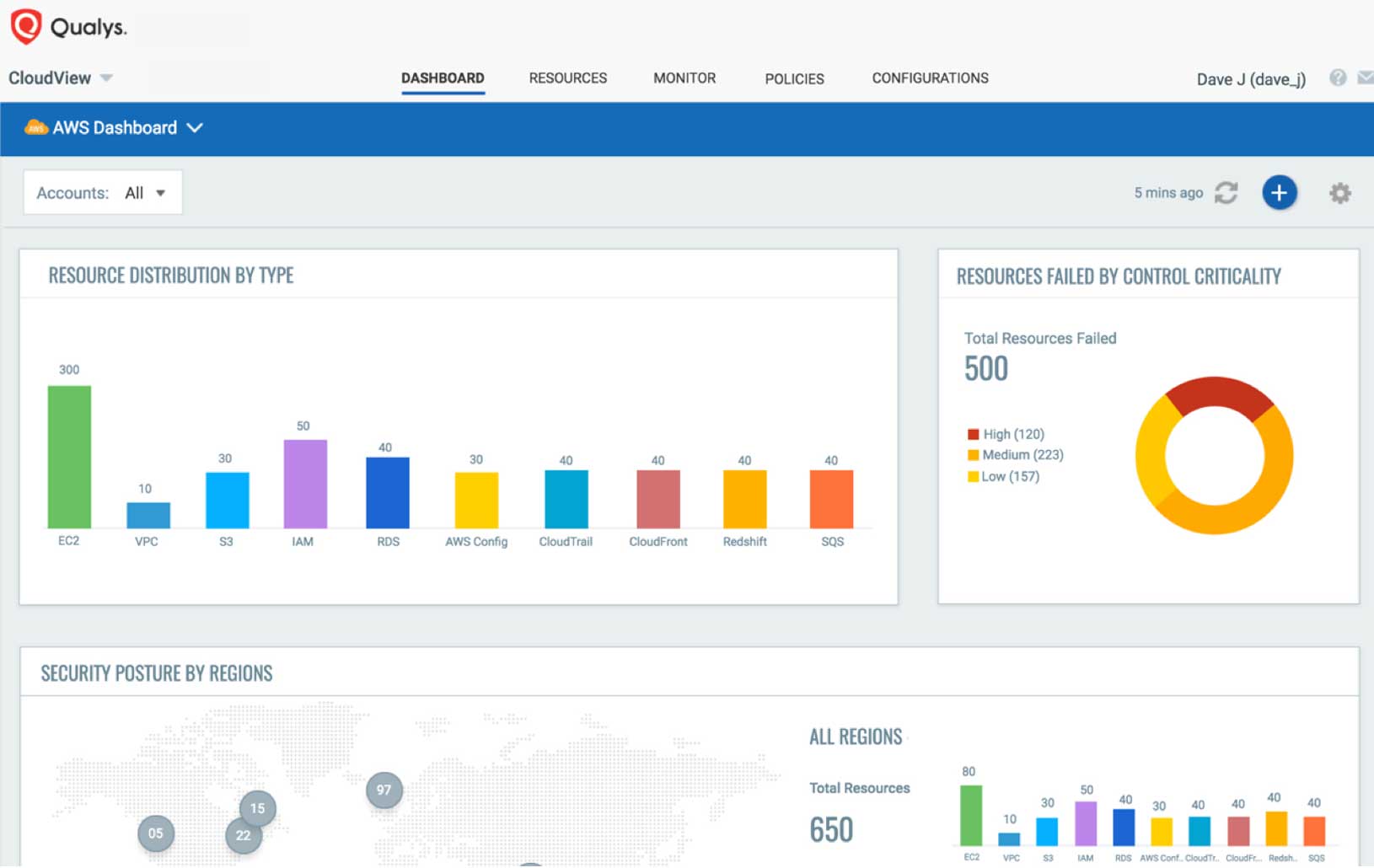
Visibility of your AWS deployments
Total visibility of your AWS cloud infrastructure and workloads through a central “single-pane-of-glass” interface.
360-degree view of all AWS assets across multiple accounts, regions from a centralized UI
Lower cost
Ease of use
Nothing to install or manage

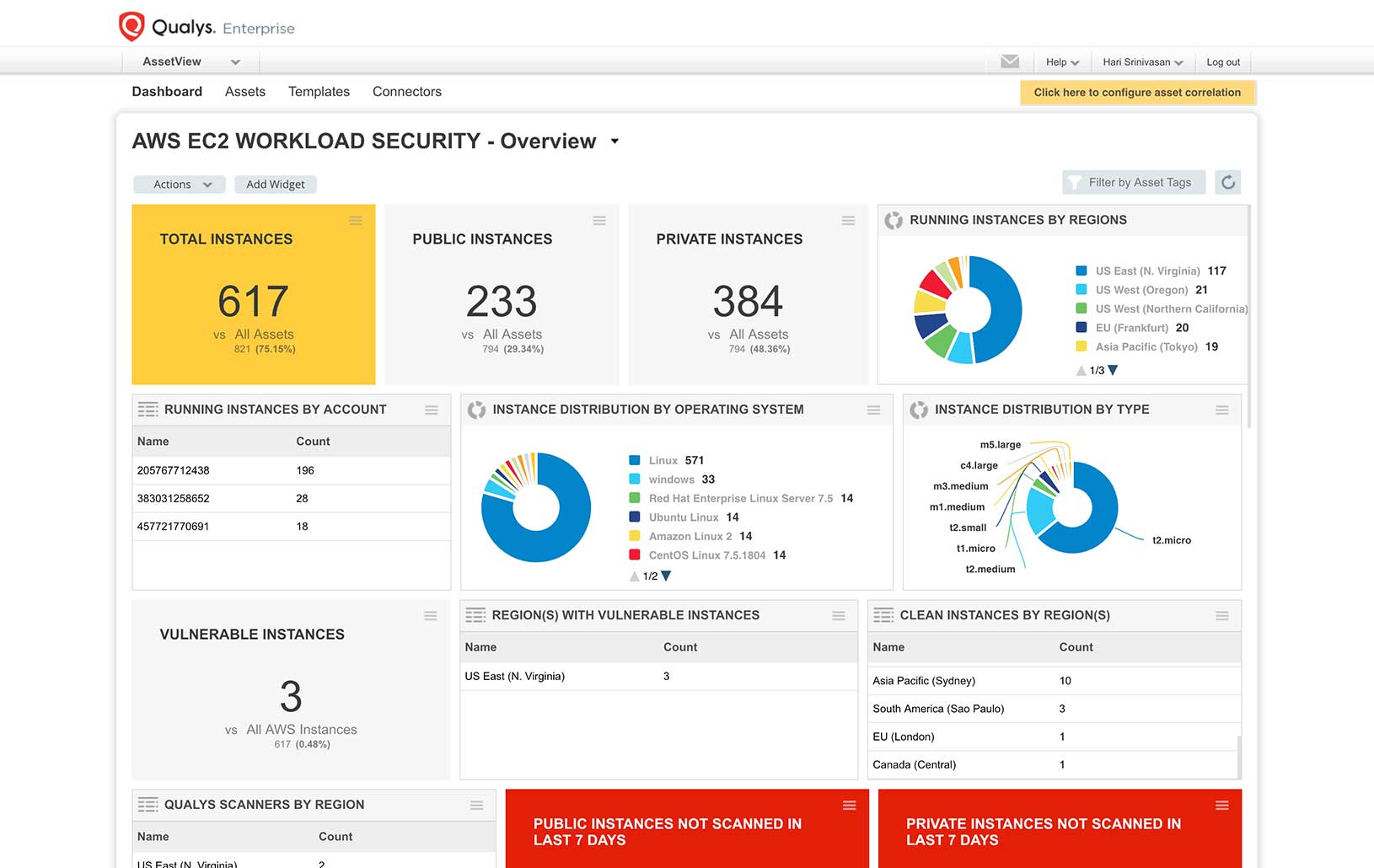
AWS workload security
Improve risk detection, prevention and response by performing a full set of security and compliance checks on your EC2 Instances, databases and web applications.
Vulnerability management
Policy compliance
File integrity monitoring
Indication of compromise
Web app scanning / firewall
Asset inventory and assessment
Other critical tasks

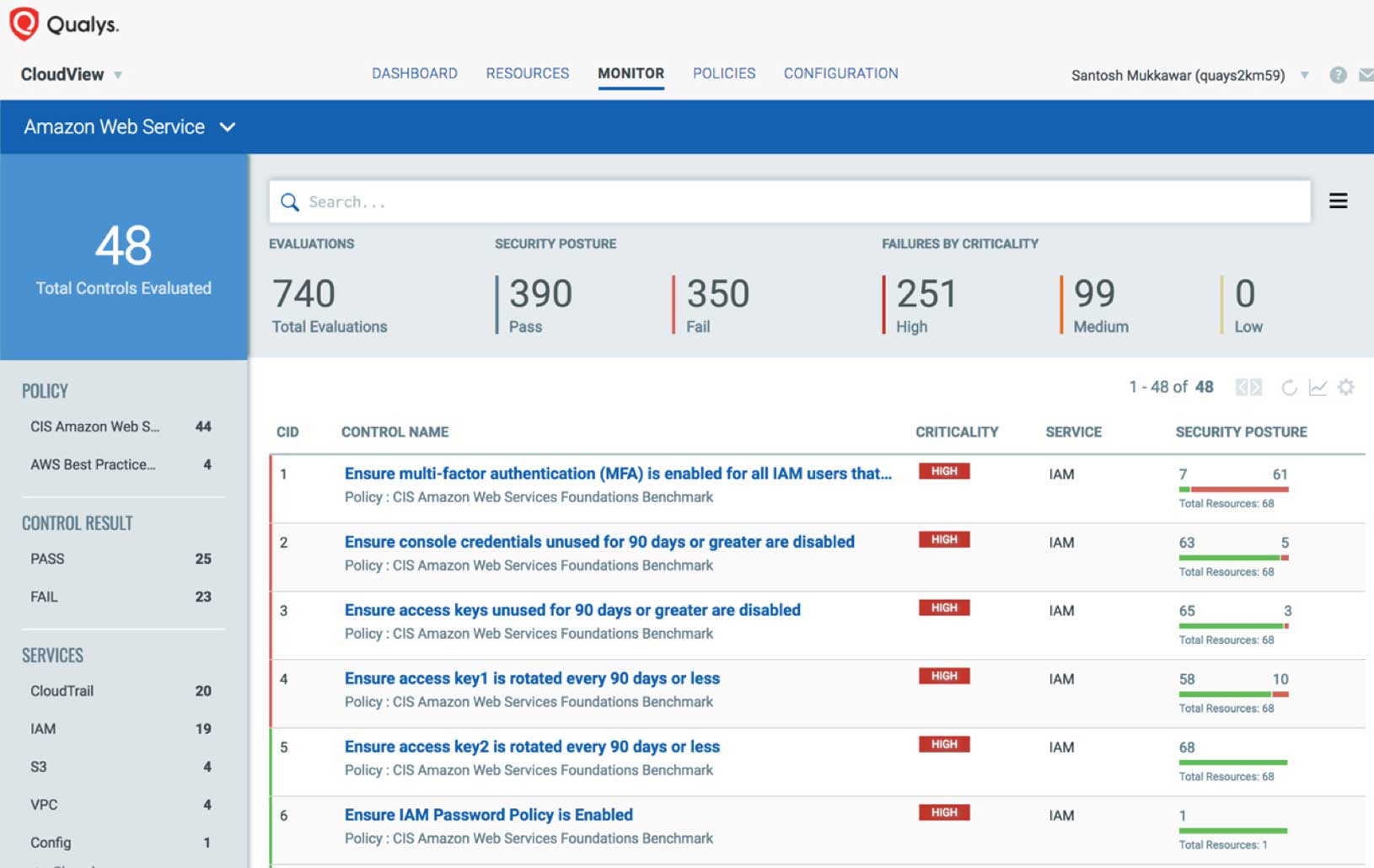
AWS infrastructure security
Monitor and assess your AWS environment against the CIS (Center for Internet Security) AWS Foundations Benchmark. Identify threats caused by misconfigurations, unauthorized access, and non-standard deployments. Get access to clear remediation recommendations so that you can maintain a solid security posture across your AWS resources like VPC, Security Groups, S3, IAM Users and RDS through automated, continuous assessments.

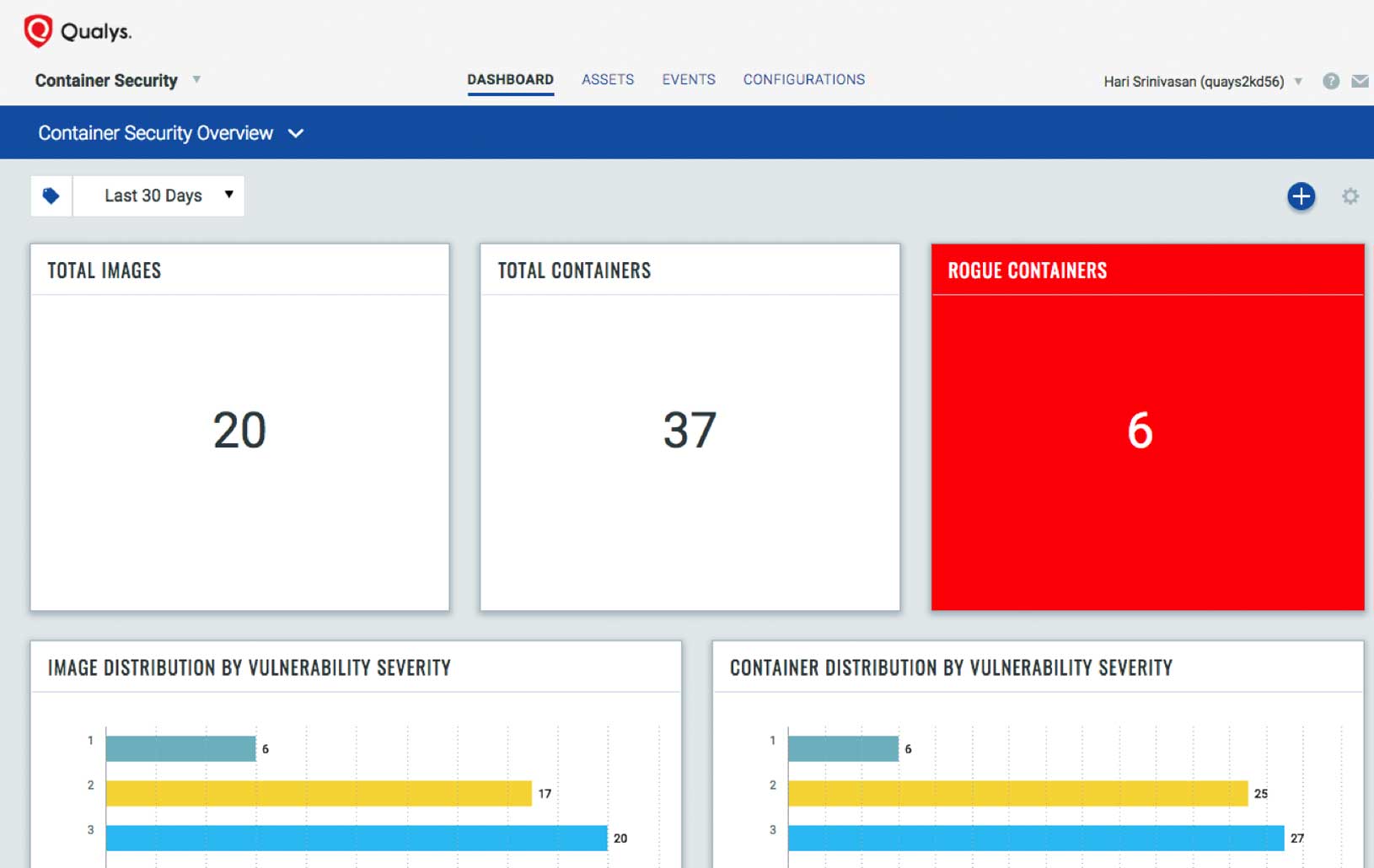
AWS container security
Qualys Container Security (CS) provides security coverage from the build to the deployment stages. Monitor and protect container-native applications on AWS without disrupting your existing Continuous Integration and Deployment (CI/CD) pipelines. Assess the contents of container images for vulnerabilities, control which images are deployed, gain visibility into runtime application activity, and also automatically enforce normal application behavior.
Qualys CS detects vulnerabilities and compliance issues with Docker images in the build pipeline and in AWS ECR, identifies behavioral anomalies and protects container runtimes deployed on AWS ECS, EKS and Fargate.

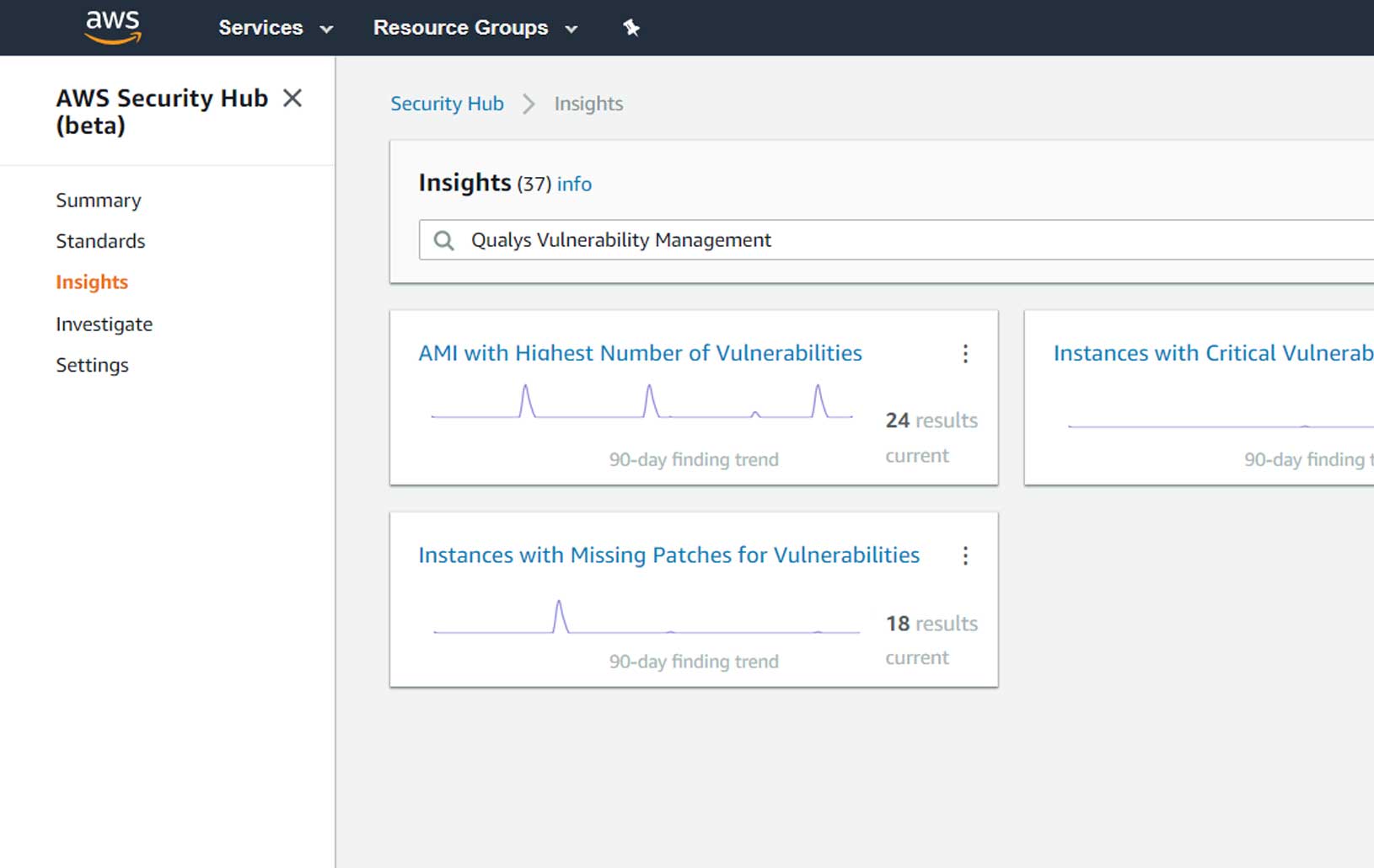
Native integration with AWS Security Hub
Natively integrate findings from the Qualys Vulnerability Management, Policy Compliance and Cloud Security Assessment apps into AWS Security Hub. Get real-time visibility into your security and compliance posture directly in the AWS console. Benefit from insights gained from the correlation of Qualys information with other data in AWS Security Hub to enable faster detection and prioritization of risks in AWS environments, enabling rapid automated remediation actions.

DevOps security in AWS
Enterprise TruRisk Platform, with its robust APIs and native integrations with key DevOps tools, lets you build security into every function in the CI/CD tool chain. This allows developers and ops staff to do security checks, and enables security teams to provide support at the pace of DevOps. Qualys Cloud Agents can be easily embedded into the AMIs or installed on instances. This gives you an ideal way to integrate security at the source and provide complete visibility for elastic cloud workloads. Learn how our customers have implemented secure DevOps, and how you can do it as well.

Integrating Qualys into DevOps on AWS - Building a Secure AMI Bakery
Watch presentation
Achieving Instant Visibility of Enterprise Risk Posture
Watch presentationGraviton ready
The Graviton Ready Qualys Cloud Agent provides customers cost savings on AWS’s Graviton2 ARM architecture while leveraging Qualys’ innovative Cloud Platform to protect their critical assets with integrated IT, compliance, and security. The Qualys Cloud Agent enables instant, global visibility of IT assets – with up-to-date asset configuration data for security, compliance, and response.
How we secure AWS
Enterprise TruRisk Platform sensors are always on, giving you continuous 2-second visibility of all your AWS assets. Remotely deployable, centrally managed and self-updating, the sensors come as physical or virtual appliances, or lightweight agents. Qualys Container Security and Web Application Firewall complement the sensors.
AWS Connector
Sync AWS EC2 instances, resources and their associated metadata
Virtual Scanners
Remotely scan instances across VPCs and Regions with pre-authorized scanners
Internet Scanners
Perform fast and efficient external scans
 Learn more about Qualys TotalCloud
Learn more about Qualys TotalCloud