Qualys VMDR for Mobile Devices
Extending the Power of VMDR to Mobile Devices
E-mail our sales team
call us at 1 (800) 745-4355.
or schedule a demo.


Manage the security of your Android and iOS/iPadOS devices across the enterprise
As we move to a mobile-first world where mobile devices connect to the network, enterprises face a new set of security challenges and risks.
Qualys' all-in-one Vulnerability Management, Detection, and Response (VMDR) solution extends its power to mobile devices. It provides in-depth inventory of mobile devices and their data, real-time vulnerability and misconfiguration detection, and built-in remediation with patch orchestration for all Android and iOS/iPadOS devices across the enterprise.


An end-to-end solution for mobile device security
- Inventory and normalize all Android and iOS/iPadOS device data, including OS version, apps installed, CA certificates, system information, etc.
- Check for misconfiguration issues, including critical settings like geolocation, activation lock, Bluetooth status, etc.
- Detect vulnerable devices, with outdated, rooted, or jailbroken OSs, or apps with critical vulnerabilities.
- Stop risky behavior by detecting devices connected to unsecured WiFi hotspots, etc.
- Take "over-the-air" remediation action like locking a user's screen, resetting a device, removing or updating an app, etc.

Built-in Workflow for Mobile Device Protection
Discover, assess, prioritize, and remediate vulnerabilities and misconfigurations in real time, across mobile devices — all from a single solution.
Highlights
Try it Free for 30 Days
Get full access to Qualys Vulnerability Management, Detection & Response (VMDR) with mobile device coverage. No credit card needed.
By submitting this form, you consent to Qualys' privacy policy.
Features
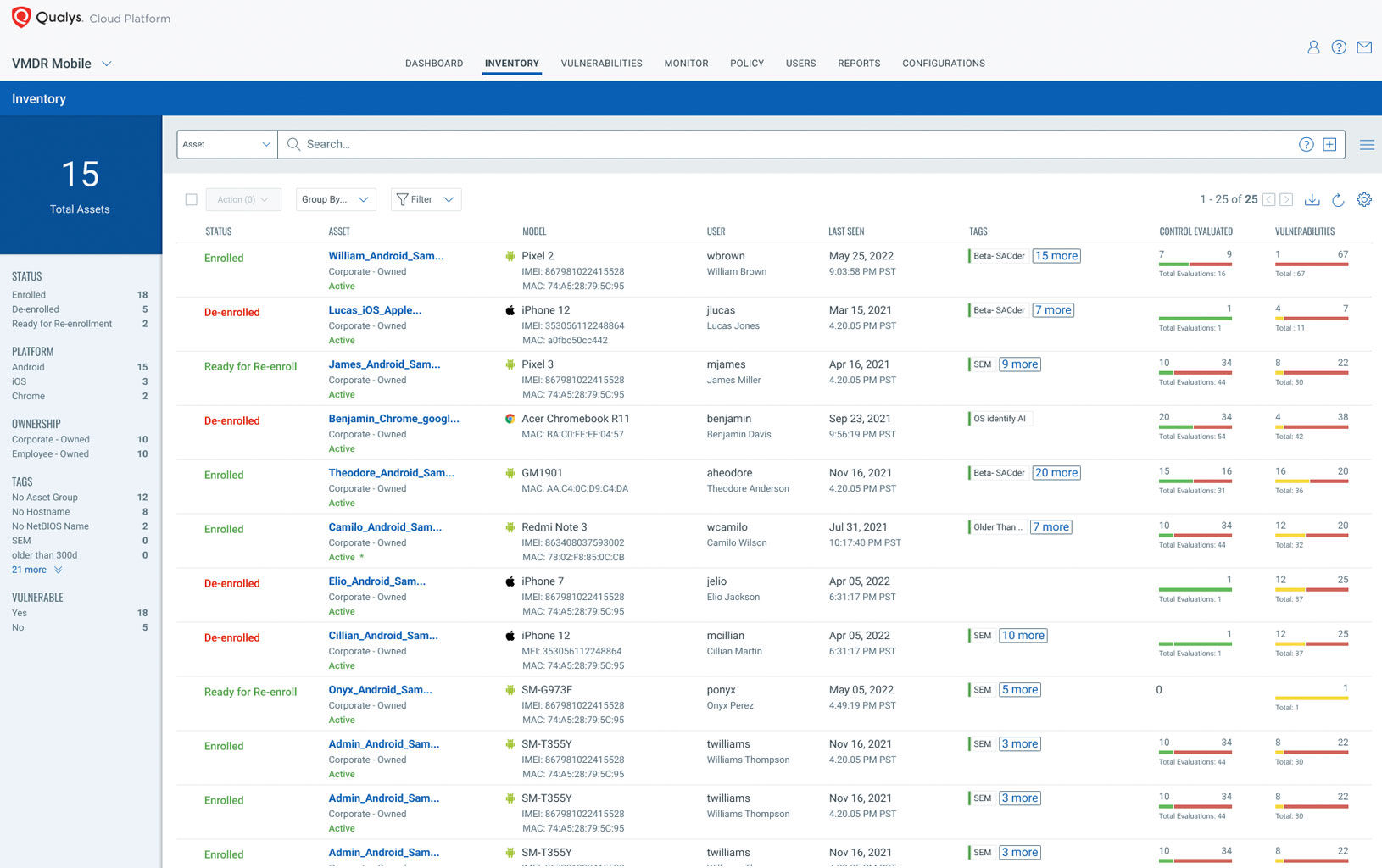
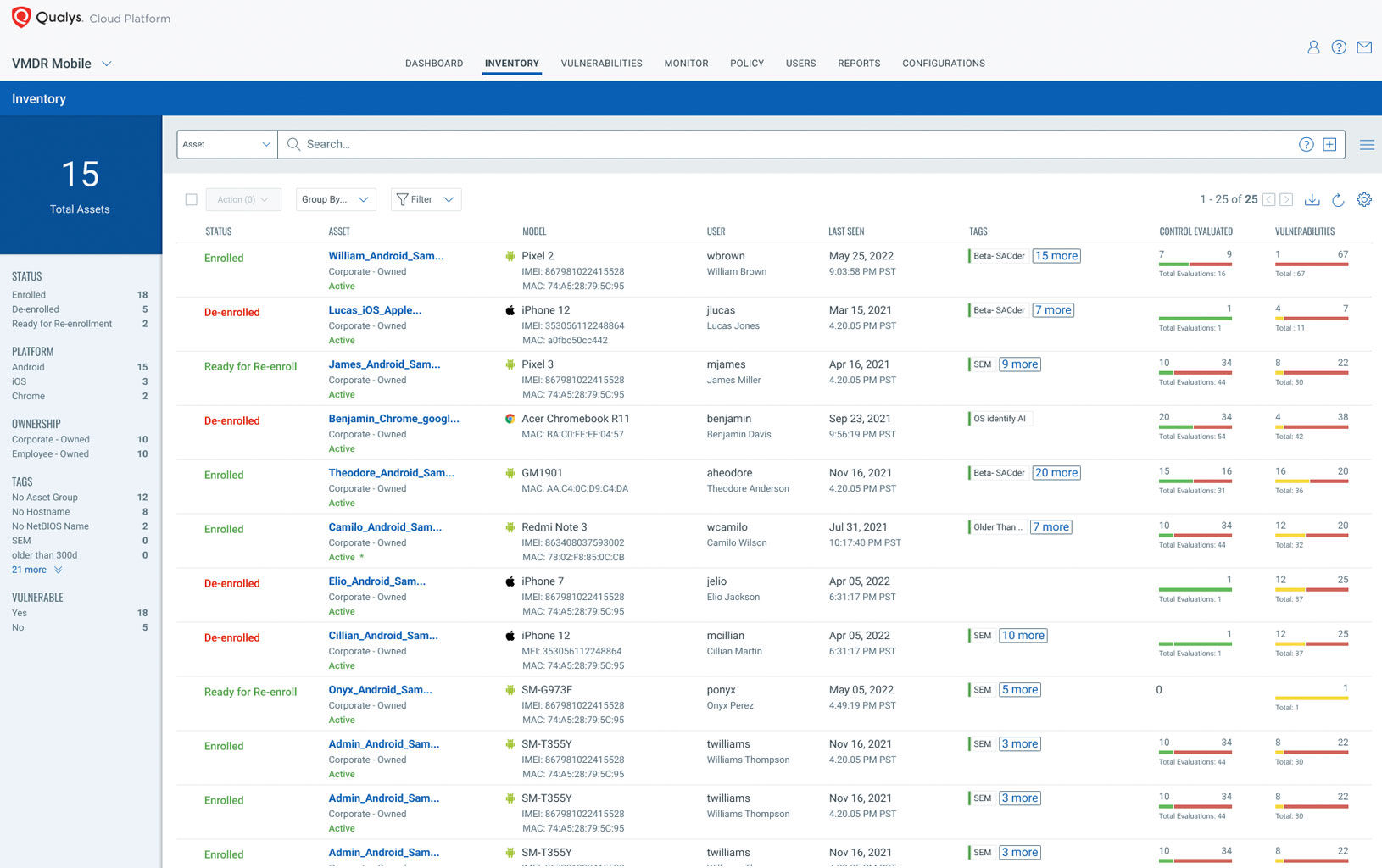
Global, in-depth mobile device inventory
To secure mobile devices, you first need visibility. Qualys VMDR for Mobile Devices provides the visibility you need to continuously inventory all Android, iOS, and iPadOS devices, providing clean, comprehensive, reliable data.
-
Easy onboarding: Quickly enroll devices by installing the Qualys Cloud Agent and scanning a QR code.
-
In-depth device data: Qualys’ lightweight Cloud Agent (available on Google Play Store and Apple App Store) collects hundreds of mobile data points such as device type, OS version, specifications, network, installed apps, and CA certificates.
-
Normalization and categorization: Standardize and classify mobile device data in your environment for every manufacturer name, product name, model, software version, and much more.
-
End-of-life Management: Manage the mobility lifecycle of Android and iOS devices across manufacturers and OS versions.
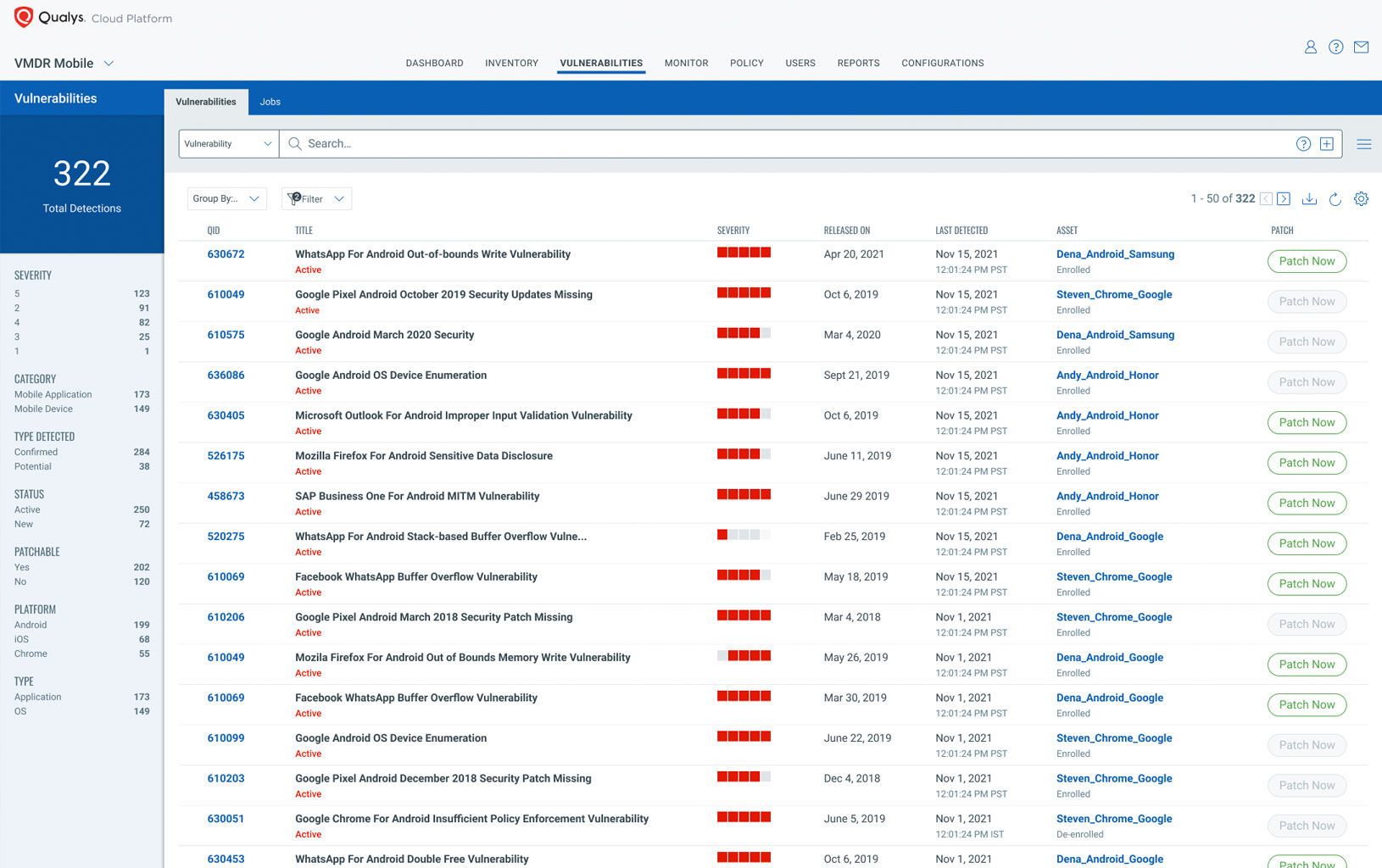
Continuous detection of exploitable vulnerabilities and misconfigurations
Qualys VMDR for Mobile Devices continuously detects vulnerabilities and CVEs with exploits, as well as critical settings and misconfigurations that can be exploited.
-
Comprehensive vulnerability coverage: Continuously assess vulnerabilities using the most comprehensive signature database in the industry across Android, iOS, and iPadOS devices and the apps they use.
-
Continuous misconfiguration assessments: Expand your vulnerability management program by continuously monitoring critical mobile device configurations as recommended by the National Security Agency (NSA) and best practices with the Center for Internet Security (CIS) configuration management (available Q2 2021). For example, detect devices connecting to unsecured WiFi hotspots.
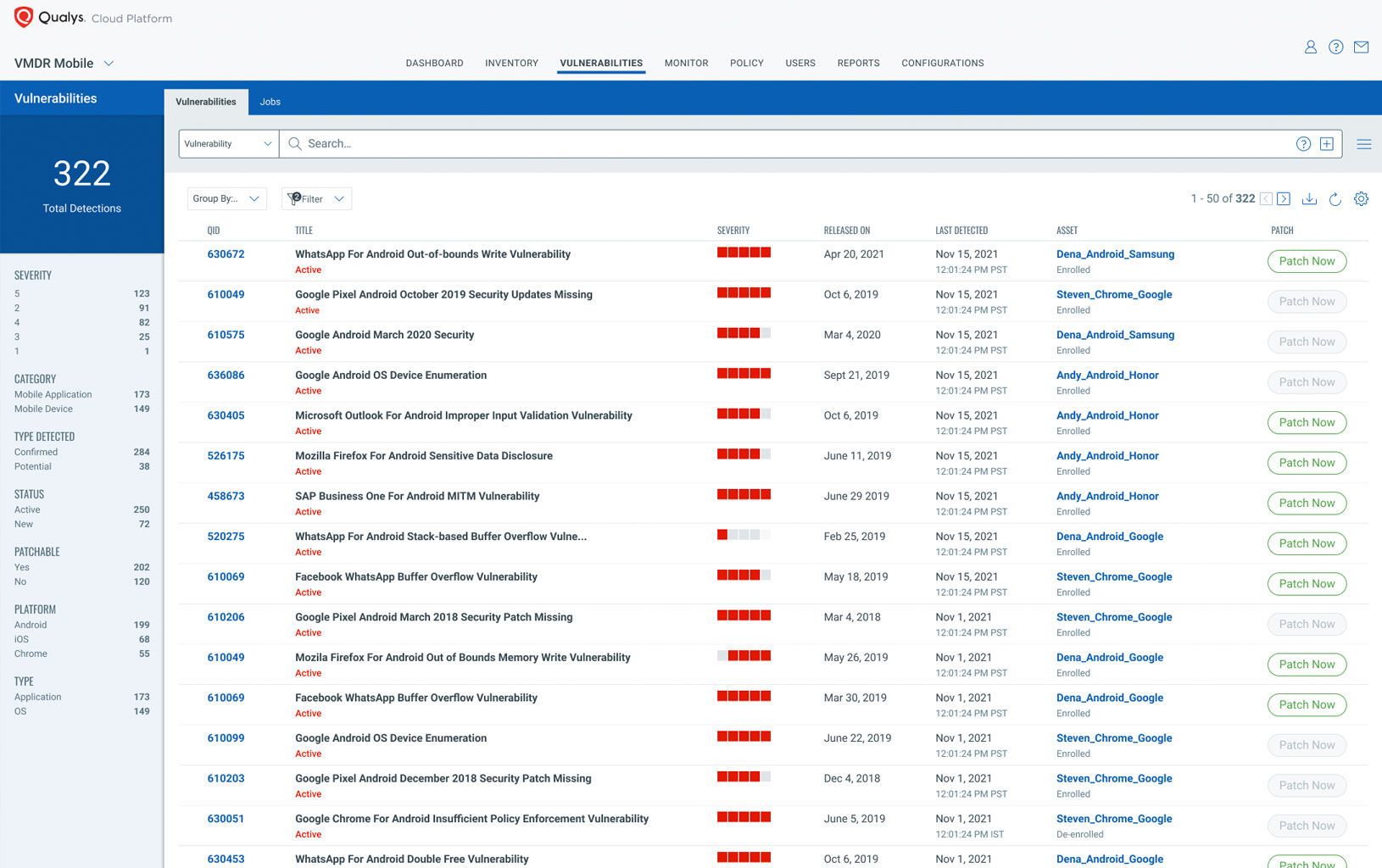
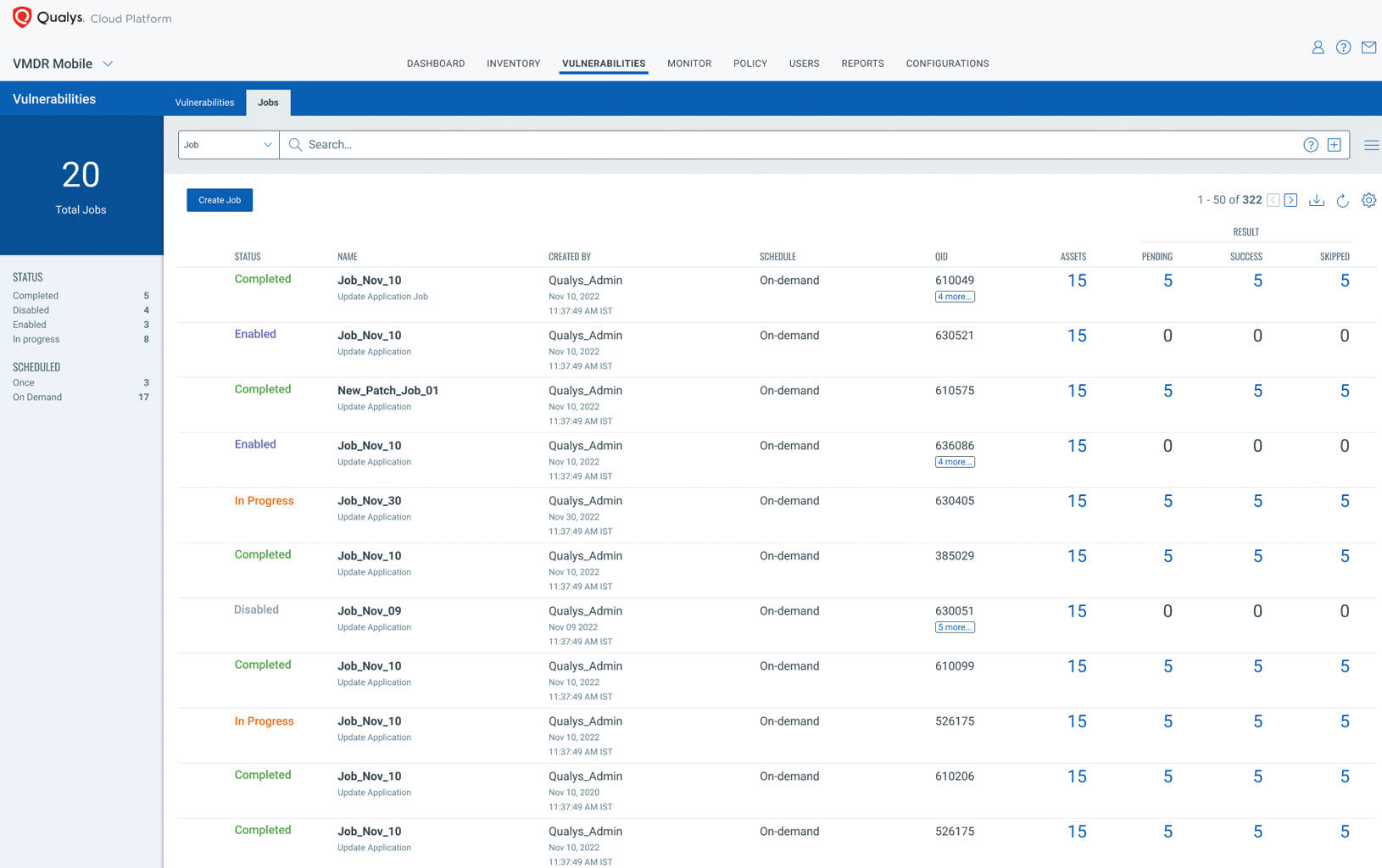
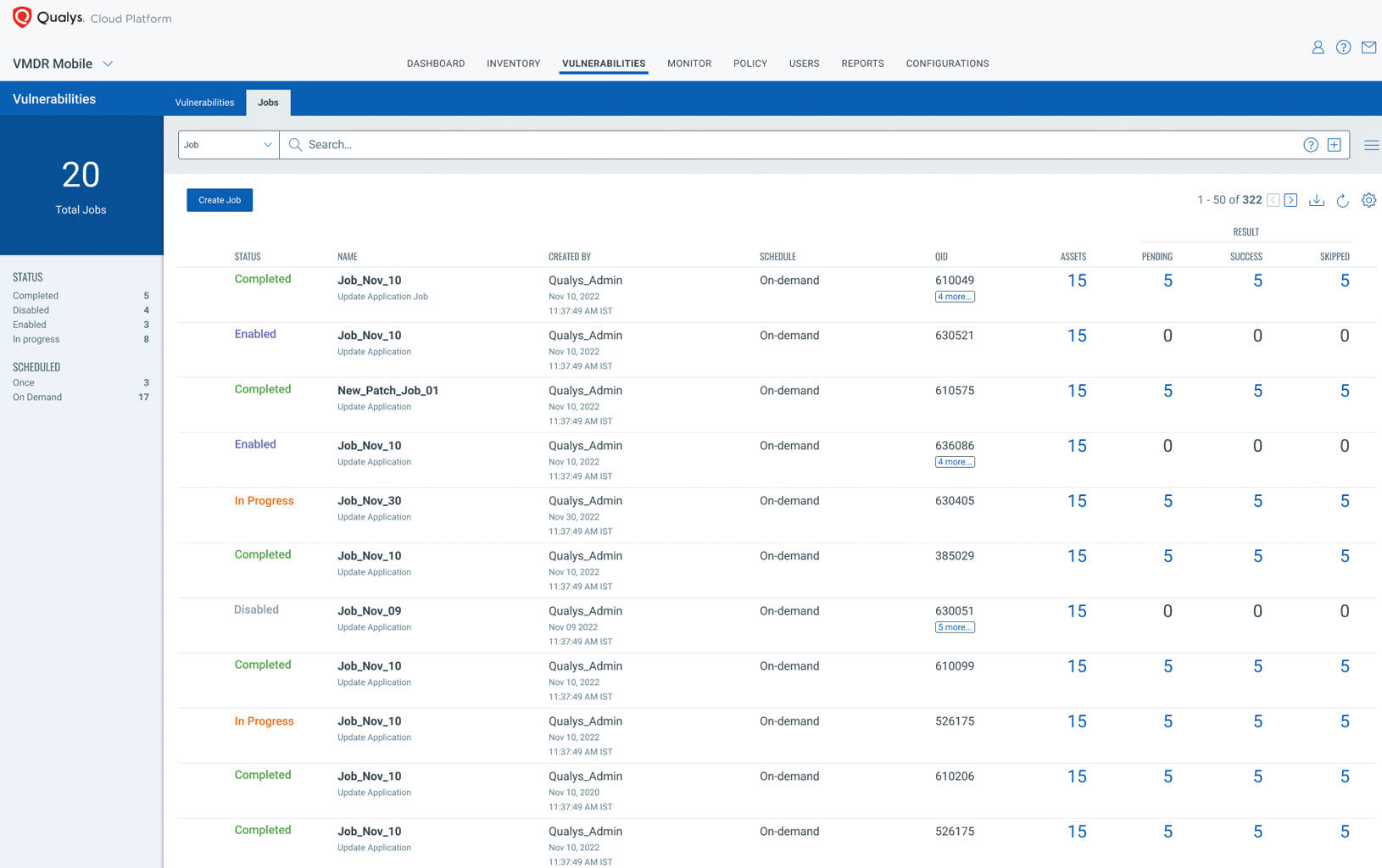
Over-the-air response
Decrease time to remediate by simultaneously performing actions remotely on at-risk mobile devices, including:
-
Uninstall or update vulnerable apps using correlated patches with the correct OS and app versions.
-
Send push notifications to mobile devices for remediation action.
-
Lock devices.
-
Reset devices to factory settings.
-
Change passcodes.

Powerful dashboards
Get the full perspective of all the data to act on insights. Qualys’ interactive, customizable dashboards provide a real-time holistic view of your mobile device data, vulnerabilities, and misconfigurations – all from a single-pane-of-glass interface.
-
Create multiple dashboard views.
-
Build interactive dashboard widgets from queries that are interesting or often used.
-
Drill down to details on events, mobile devices, users, and trends, and zero in on potentially damaging changes.
-
Displays widget data in various ways using graphs, tables, and charts.
-
Establish thresholds and alerts for monitoring important activities or benchmarks.

Try Qualys VMDR for Mobile Devices for free.
Start your free trial today and assess your risk. Everything is in the cloud and ready to run. Email us to request a quote, or call us at 1 (800) 745-4355.