No investment or resources required
Stay Continuously Audit Ready
Policy Audit
Eliminate audit complexity with continuous monitoring, automated remediation workflows, and risk-based insights - all in a single platform.
Discover how Qualys can transform audit preparation making them more efficient, accurate, and cost-effective.
Take immediate action
Turbocharge vulnerability management
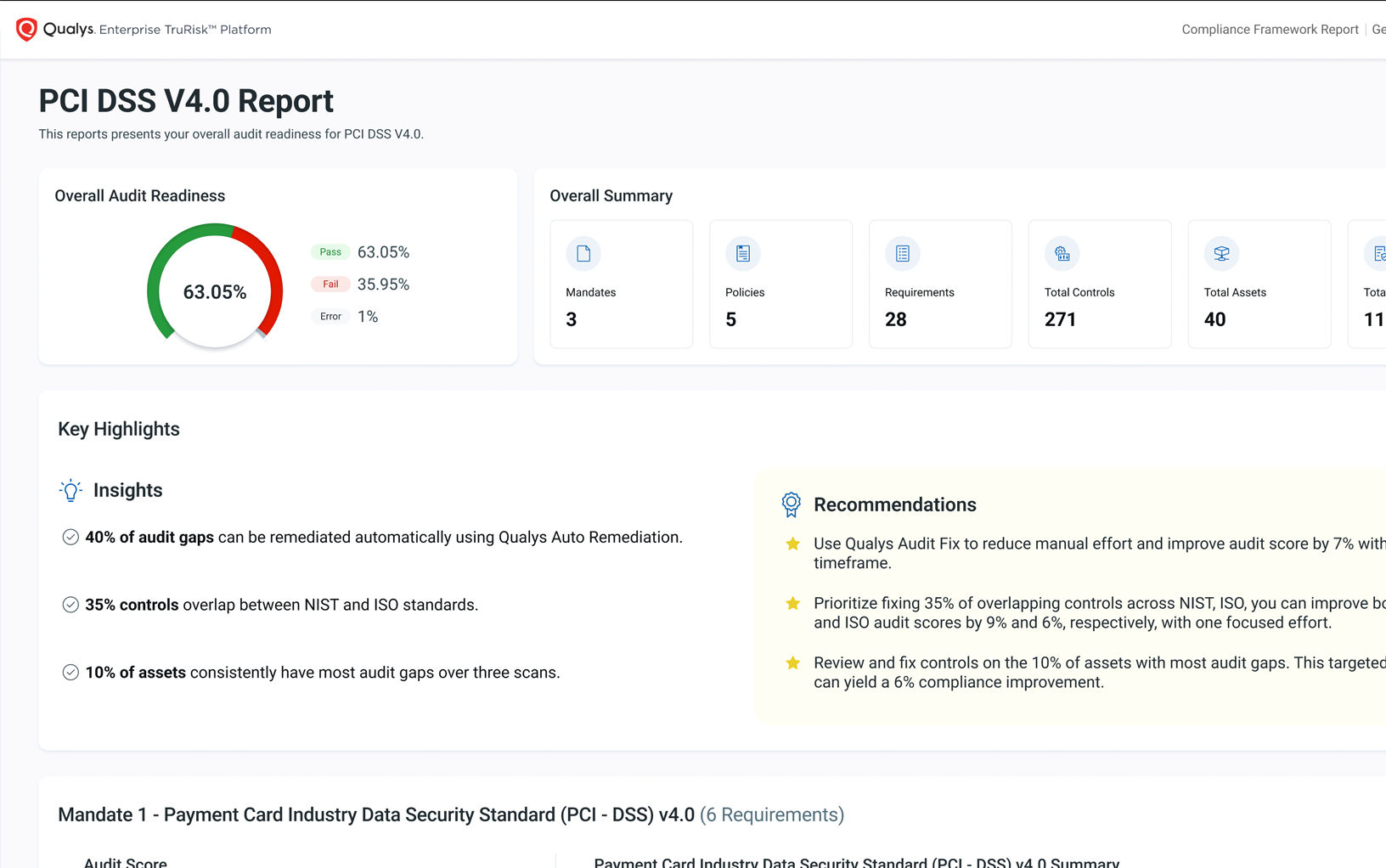
Get more than a snapshot—get direction. The Executive Audit Readiness Report pinpoints gaps and delivers prescriptive insights to strengthen compliance and improve audit outcomes.
Reduce Risk & Stay Continuously Audit Ready
Go beyond configuration assessments to simplify audits and reduce compliance risk with automated evidence collection, mandate-based controls, and seamless integration.
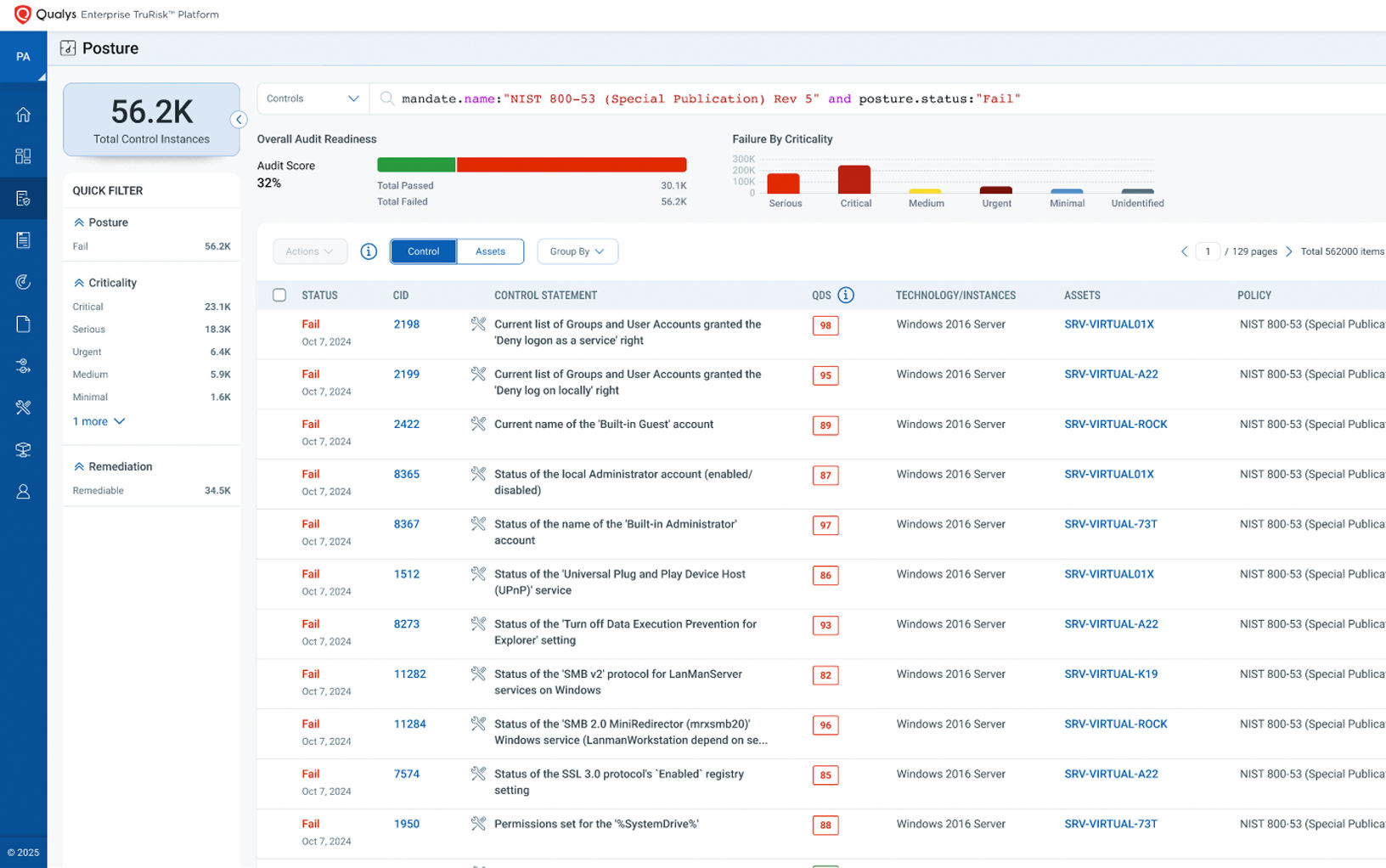
Prioritize Compliance Risks with Precision
Align remediation with:
- Audit Impact – Address misconfigurations that directly affect compliance outcomes
- Business Criticality – Focus on assets that are essential to operations.
- Control Severity – Prioritize gaps based on risk exposure and compliance weight.
- Ransomware Exposure – Reduce risks tied to exploitable misconfigurations.

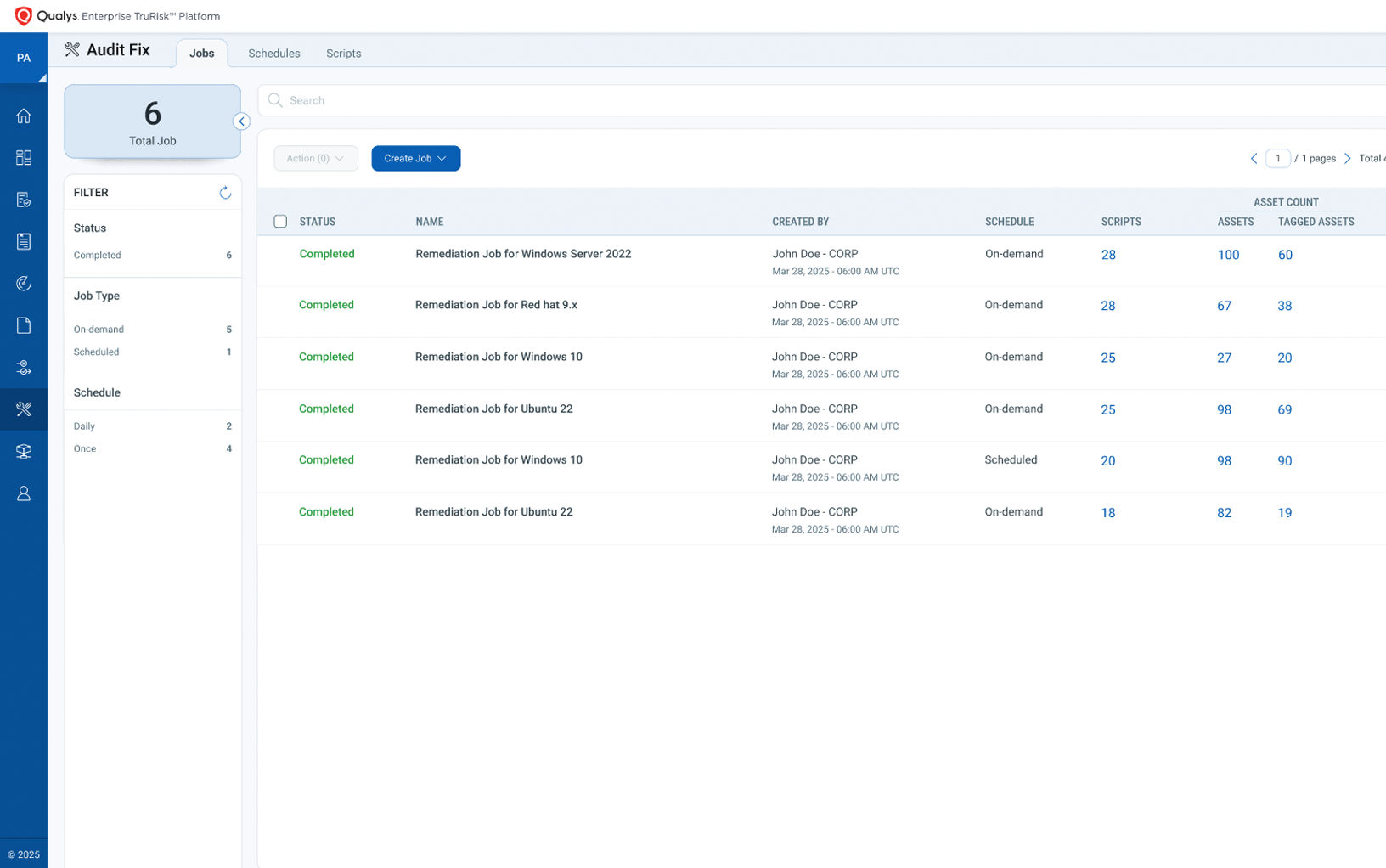
Automate End-to-End Compliance & Remediation
Ensure Compliance Visibility & Audit Success
Why Qualys?
Stay Continuously Audit Ready with a Unified Compliance Platform
Reduce Compliance Costs & Manual Effort
Identify & Close Compliance Gaps Faster
Improve Audit Effectiveness & Accuracy
Eliminate Regulatory Complexity Across Mandates
Ensure Continuous Audit Readiness
Accelerate Remediation
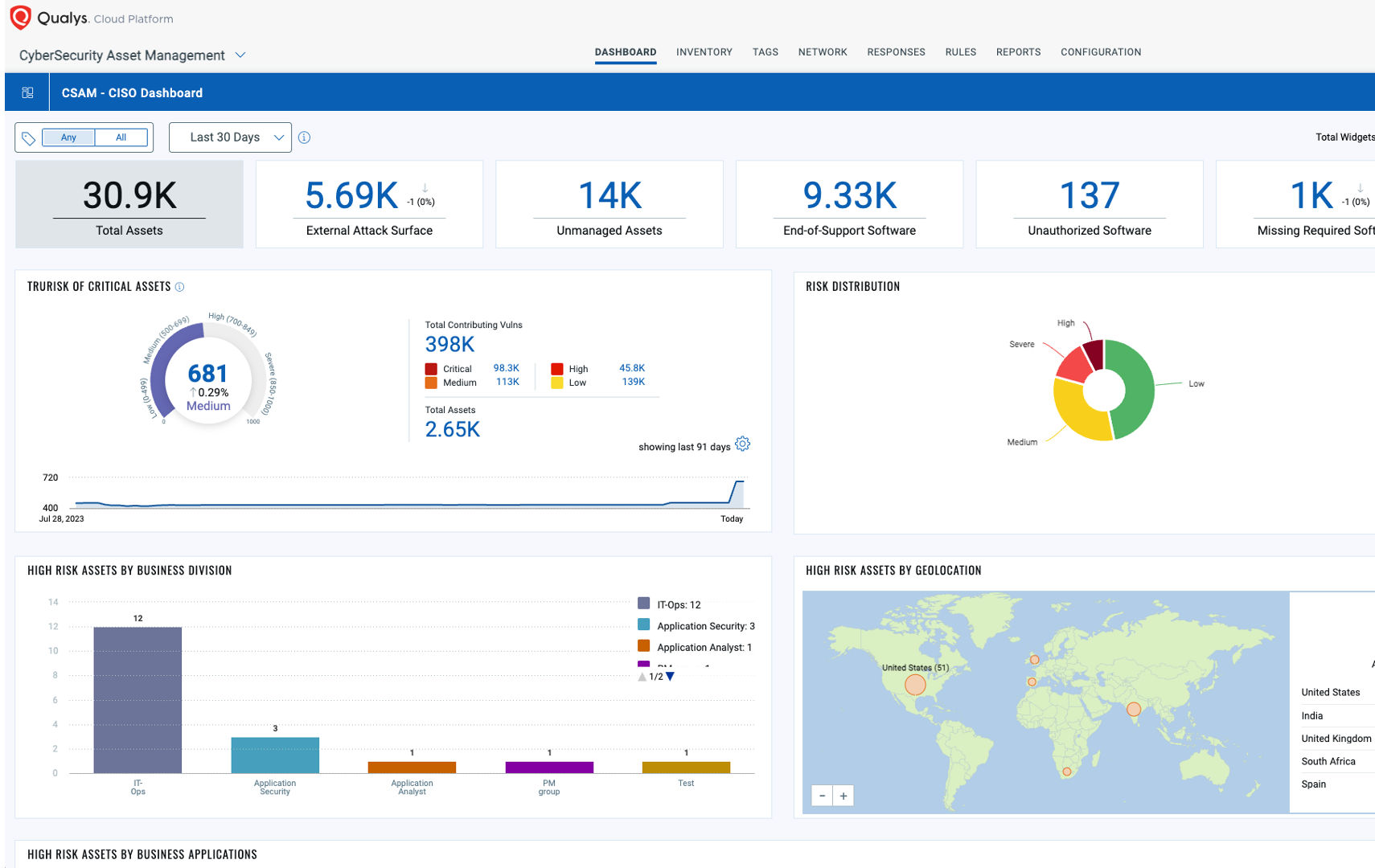
Powered by the Enterprise TruRisk™ Platform
The Enterprise TruRisk™ Platform provides you with a unified view of your entire cyber risk posture so you can efficiently aggregate and measure all Qualys & non-Qualys risk factors in a unified view, communicate cyber risk with context to your business, and go beyond patching to eliminate the risk that threatens the business in any area of your attack surface.