Endpoint Security: Defined
What is an Endpoint?
An endpoint is a remote, connected device that communicates with a network, or networks. Examples of endpoints include:
- Smartphones
- Tablets
- Laptops
- Desktops
- Servers
- Human-Machine Interfaces (HMIs)
- Workstations
- Wearable connected devices, smart meters, and other IoT devices
- Remote Terminal Units (RTUs), Controllers, and other operational technology (OT)
What is Endpoint Security?
Work-from-anywhere culture has changed the nature of the typical enterprise network from a configuration where the security perimeter was found on-premises surrounding a central datacenter, to one that is defined by distributed and mobile endpoints that are connecting to a multi-cloud environment. Thus, modern security practices must adapt to bring the security perimeter to all endpoints, wherever they may be.
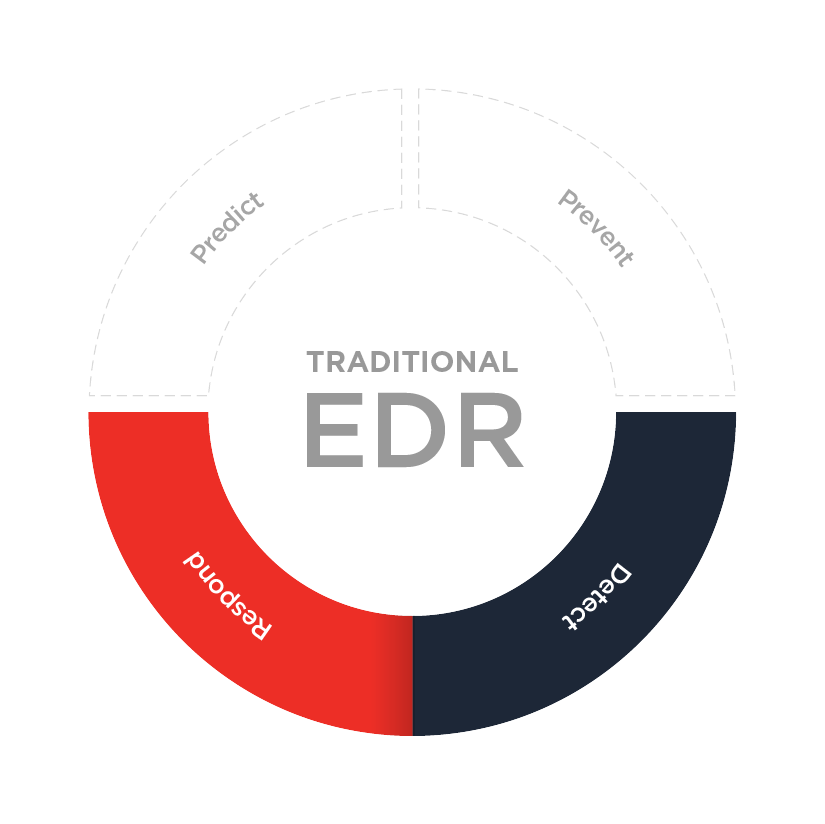
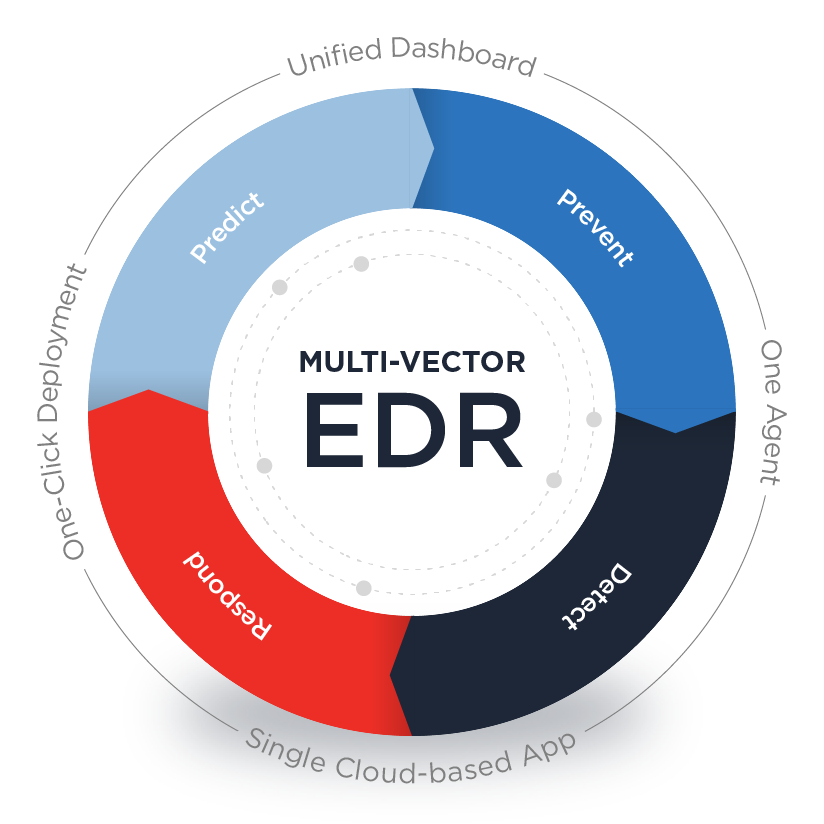
Common endpoint security solutions include Endpoint Protection Platforms (EPP), Endpoint Detection and Response (EDR), and Managed Detection and Response (MDR).
Why Endpoint Security is Important
An endpoint security strategy is essential because any remote endpoint can be the entry point for an attack, and the number of endpoints is only increasing with the rapid pandemic-related shift to remote work. According to a Gallup Poll, a majority of US workers were remote in 2020, with 51% still remote in April 2021. The risks posed by endpoints and their sensitive data are a challenge that’s not going away.
The endpoint landscape is constantly changing, and businesses of all sizes are attractive targets for cyberattacks. This is common knowledge, even among small businesses. According to a study conducted by Connectwise in 2020, 77% of 700 SMB decision makers surveyed worry they will be the target of an attack in the next six months.
According to the FBI’s Internet Crime Report, they received an increase of 300,000 complaints over 2019, with reported losses topping $4.2 billion. The Verizon 2021 Data Breach Investigations Report found: “Servers are still dominating the asset landscape due to the prevalence of web apps and mail services involved in incidents. As social attacks continue to compromise people (they have now pulled past user devices), we begin to see the domination of phishing emails and websites delivering malware used for fraud or espionage.”
Each data breach costs an average of $3.86 million globally, with the United States averaging $8.65 million per data breach according to Ponemon’s Cost of a Data Breach Report 2020 (commissioned by IBM). The study identified the biggest financial impact of a breach was “lost business,” making up almost 40% of the data breach average cost.
Protecting against endpoint attacks is challenging because endpoints exist where humans and machines intersect. Businesses struggle to protect their systems without interfering with the legitimate activities of their employees. While technological solutions can be highly effective, the chances of an employee succumbing to a social engineering attack can be mitigated but never entirely prevented.
Qualys Endpoint Security Solutions:
Qualys offers Multi-Vector EDR, providing comprehensive threat protection across the entire enterprise hybrid IT environment. Thanks to the native telemetry built with the Enterprise TruRisk Platform, combined with an open platform approach supporting third-party integrations, Qualys has an endpoint security solution for you.