Qualys ProtectIT 30-Day Free Trial
Bringing the power of the Enterprise TruRisk Platform to small and mid-sized businesses
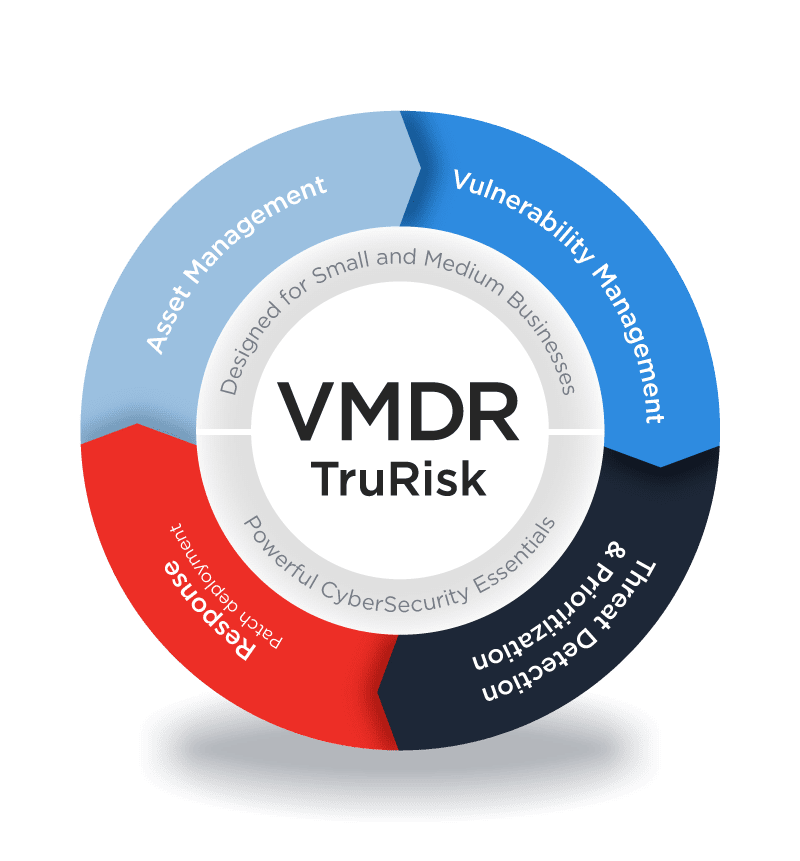
The Qualys TruRisk ProtectIT package combines Qualys Endpoint Protection with Patch Management and VMDR capabilities. Qualys Patch Management can be used to patch and apply post-patch configuration changes to Windows, Linux and Mac operating systems, mobile devices, and 3rd-party applications from a large variety of vendors, all from a central dashboard. Qualys Endpoint Protection consists of machine learning (ML), behavior-based anti-virus, and Qualys Endpoint Detection and Response (EDR), combining signatures, machine-learning models, behavior technologies, anti-virus blocks zero-day attacks, ransomware, and phishing. Endpoints are continuously monitored and remedied for suspicious activity by EDR with a single agent to handle real-time incident response and remediation.
Low TCO with Flexible Pricing
Easy to deploy with no hardware to buy or manage. In addition, comes with software auto updates.
Automated Vulnerability Assessment and Remediation
Extend remediation and patch vulnerabilities up to 40% faster than other solutions.
Protection Against Ransomware
Automatically block malware and ransomware infections.
Compliance and Enforcement
Get templated reports and compliance controls for nearly all compliance and regulatory directives, including PCI, HIPAA, CIS, and more
Create your free account
By submitting this form, you consent to Qualys' privacy policy.
Anti-virus & Anti-malware Protection
Antivirus & protection from advanced attacks
Consolidate IT and Security Tools for vulnerability assessment, remediation and ransomware protection
Rapid investigation, analysis of incidents to prioritize risk to critical assets & remediate risk, via integrated EDR
Remediation and Patch Management
Consolidate IT and Security Tools for vulnerability assessment and remediation
Automate patching for cloud and on-prem assets (operating systems & 100+ 3rd party applications)
Set and forget patching to automatically remediate ransomware, and malware exploitable vulnerabilities
Cut remediation time in half. Up to 40% faster
Comprehensive Risk-Based Vulnerability Management
Know all assets on-prem or cloud, and classify them based OS, application and 100+ attributes.
Comprehensive risk-based vulnerability management solution.
Detect critical threats up to 5x faster by leveraging Risk-Based Prioritization using 25+ threat intelligence feeds.
Maintain Security hygiene for all workstations, servers, databases, and other technologies based on CIS benchmarks.
Monitor SSL certificates for expiry. Prevent business outages, inventory certificates, and renew expired certificates.
PCI assessment with approved ASV scan