VS
VS 
Say goodbye to your fragmented cyber risk program
Shift away from the platform-by-portal method of Tenable and embrace the streamlined efficiency of Qualys. Measure, communicate, and eliminate cyber risk across your extended enterprise the Enterprise TruRisk™️ Platform seamlessly integrated with External Attack Surface Management (EASM), Cloud Security, and Patch Management solutions.
Measure Risk
6x faster
than competitive VM platformsCommunicate Risk
200K+ Vulnerabilities
sourced from 25+ threat intelligence feedsEliminate Critical Risk
60% faster
with a one-click workflow and ITSM integrationsIn today's dynamic business landscape, scalability, flexibility, and seamless orchestration of asset data are essential for effective cyber risk management. While other solutions like Tenable fall short, Qualys offers a superior approach tailored to unique needs of modern enterprises.
Top 5 reasons to switch to Qualys from Tenable
Still not convinced?
The Enterprise TruRisk Platform is the only natively developed cyber risk management platform.
Because it’s built on a foundation of risk-based vulnerability management, it’s a highly scalable solution that allows businesses to add in external attack surface management, patch management, web application scanning (WAS), first-party (custom) software risk management, endpoint detection and response, policy compliance, and cloud workflow protection (CWPP) - all with the click of the mouse.
Combined with the scalability and flexibility of Qualys VMDR and TotalCloud™️ 2.0, the Enterprise TruRisk Platform provides you with a unified view of your entire risk posture by leveraging powerful functionality. Let’s compare the difference.
How Qualys compares to Tenable

|

|
Ease of DeploymentCloud-delivered or on-premises with 100% feature parity. |
PartialCloud-based service and additional platform features require managing an on-premises version of the product. |
|
Asset CoverageCovers the entire Hybrid IT landscape, on-premises servers (Windows, Linux, Mac), workstations, 25% of servers, workstations, network devices, web applications, cloud assets, cloud databases, network devices, containers, cloud instances, and containers, etc. |
PartialCovers servers, workstations, network devices, web applications, cloud assets, cloud databases, network devices, containers, cloud instances, and containers, cloud storage, smartphones, tablets, containers, and OT infrastructure. |
|
Agent SupportQualys Cloud agents can be deployed on Windows, Mac, Linux, BSD, IBM AIX, Red Hat CoreOS, Solaris, and Chrome OS. |
PartialTenable Agents support Windows, Linux, and macOS. |
|
Vulnerability IdentificationVulnerabilities are identified based on running a vulnerability test against the application/ software components using network scanners, agents, container scanners, passive scanners, and API connections. |
PartialVulnerabilities are detected by using vulnerability scanner appliances powered by Nessus. |
|
Six Sigma AccuracyQualys consistently exceeds Six Sigma with 99.99966% accuracy. |
PartialClaims Six Sigma accuracy with their Nessus but does not offer remediation capabilities at all. |
|
Comprehensive Vulnerability Coverage102K+ CVEs out of the box, including 1K+ AI-specific vulnerability detections and 16K+ deep-scanning detections for open-source software to detect openSSL, log4j, etc. |
PartialCovers 90K+ CVEs with plug-ins added within 24 hours of vulnerability disclosure. |
|
Real-time Vulnerability AssessmentThe mean time to detect new vulnerabilities is 4 hours or less. |
PartialNot clear how quickly Tenable One can detect vulnerabilities in real time. |
|
Security ConfigurationQualys VMDR offers security configuration assessment against CIS benchmarks. |
PartialNessus security configuration assessment for CIS benchmarks is not included with the Tenable One platform and requires a separate on-premises solution. |
|
Vulnerability Prioritization25+ sources of threat intelligence to assign TruRisk risk ratings to prioritize vulnerabilities based on business impact across the entire hybrid environment |
PartialA Vulnerability Priority Rating that combines threat intelligence to predict the likelihood a vulnerability is exploited. |
|
Asset Discovery and InventoryStarts from asset discovery using passive network sensors and then builds an updated asset inventory of software and hardware using agents for the entire hybrid Hybrid IT landscape. |
PartialUses a combination of discovery scans, web applications, and cloud connectors to build an asset inventory. |
|
Risk RemediationVMDR performs Patch detection as well as Patch deployment without requiring a VPN connection. |
PartialTenable One relies on third-party systems such as BigFix, SCCM, and WSUS for patching. |
|
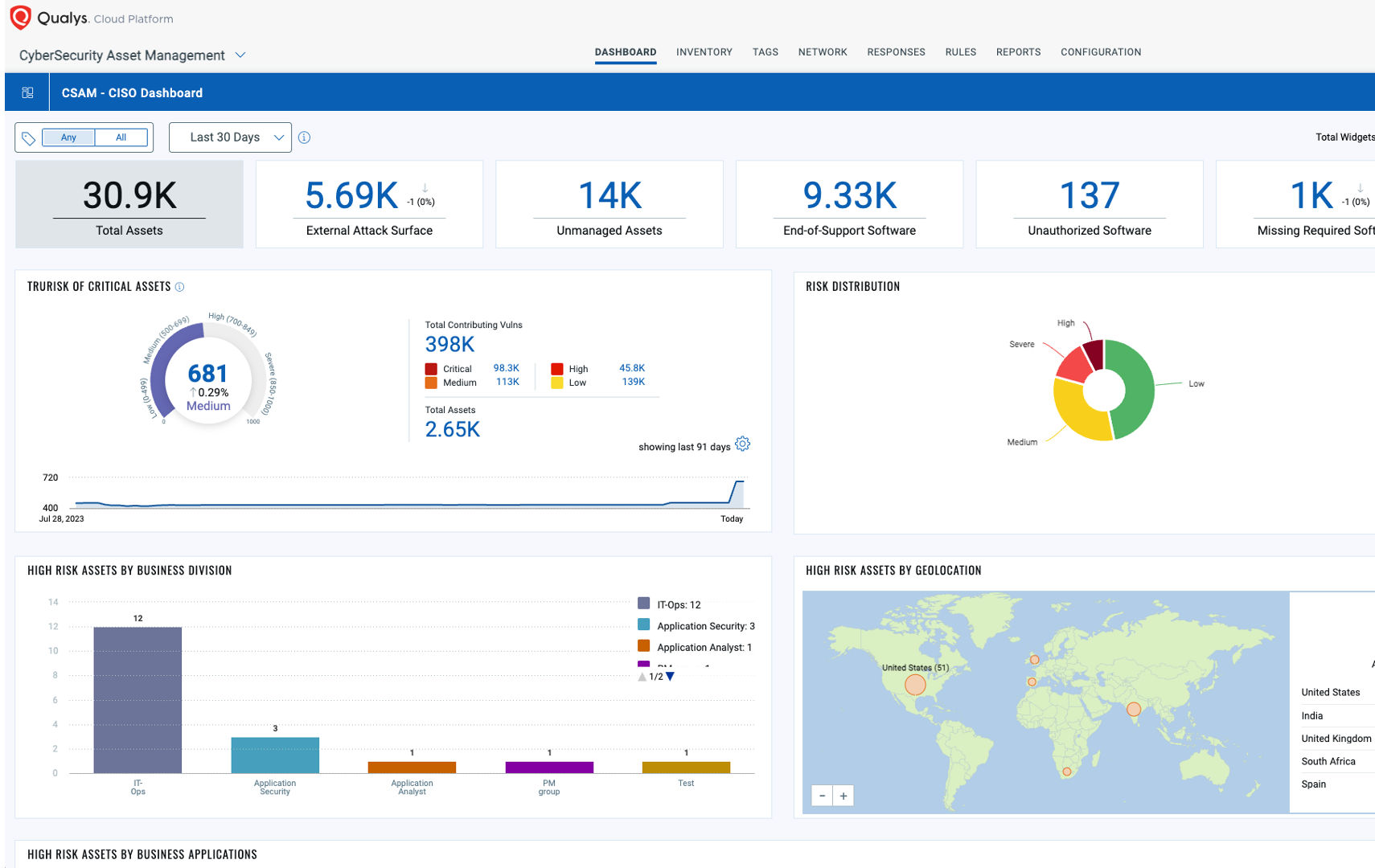
Risk ReportingReady-to-use reporting and dashboards to visualize and understand vulnerability risk across assets, business groups, and geographic locations. |
PartialGives users the ability to run reports and create customizable dashboards with eight widget types. |
|
IntegrationsSelf-contained ITSM app in the ServiceNow store to manage vulnerabilities with change management, exception, and false positive tracking. |
PartialSelf-contained ITSM app in the ServiceNow store to create vulnerability tickets but lacks change management, exception, and false positive tracking. |
Say goodbye to your fragmented approaches and hello to a unified system that maximizes your security efforts.
The Enterprise TruRisk Platform provides you with a unified view of your entire cyber risk posture so you can efficiently aggregate and measure all Qualys & non-Qualys risk factors in a unified view, communicate cyber risk with context to your business, and go beyond patching to eliminate the risk that threatens the business in any area of your attack surface.