Qualys Certificate Assessment generates certificate instance grades using a straightforward methodology that allows administrators to assess often overlooked server SSL/TLS configurations without having to become SSL experts. Certificate grades reflect the strength of the underlying application or service configuration, and pinpoint specific configuration settings that highlight the use of best practices or lack thereof. It also allows you to quickly remediate cipher suites, protocols and key exchange parameters on the underlying endpoints.
Next-generation cloud app for continuous monitoring, dynamic dashboarding and custom reporting of certificate issues and vulnerabilities
CertView
A free service from Qualys for your Internet-facing certificates

- See your SSL/TLS configuration grades
- Identify the certificate issuer
- Track certificate expiration
Qualys Certificate Assessment Highlights
Certificate grade generation
Compliance
Qualys Certificate Assessment identifies out-of-policy certificates with weak signatures or key length, and shows you how many unique Certificate Authorities were found in the environment and how many certificates each one issued.
Includes Certificate Inventory (CRI)
Working in tandem with Qualys Certificate Inventory, which is included for free, it performs continuous and complete detection and cataloging of every certificate from any Certificate Authority.
Learn MoreLook for specific certificates and grades
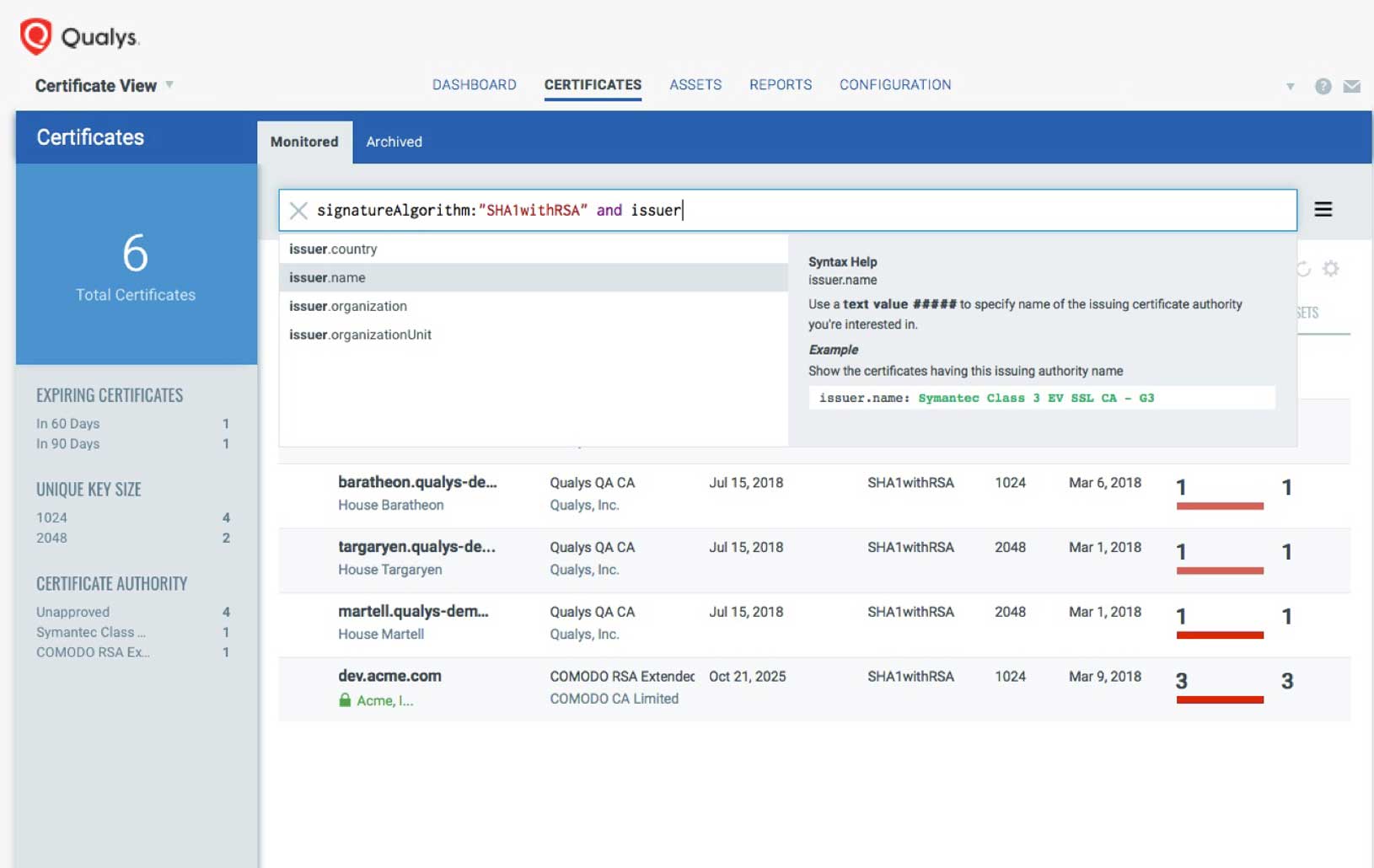
Qualys Certificate Assessment features a fast and powerful search engine to look for specific certificates, vulnerabilities, configurations and grades. Once you find certificates and configurations across your enterprise that are weak and vulnerable, you can take remediation steps immediately. The query syntax is intuitive and the product has a type-ahead feature that makes it easy to craft queries. Qualys Certificate Assessment’s search engine lets you:
Create queries with multiple variables and search criteria such as certificate signature algorithm, issuer, protocols and enabled cipher suites, so that you can look for all instances that have SHA1 certificates from a particular Certificate Authority, on assets that have SSLv3 enabled along with RC4 cipher suites
Sort, filter and save search queries
Download search results in various formats such as CSV, pdf, doc or html
Create dashboard widgets from queries that are interesting or often used

Centrally control and visualize prioritization of certificate and configuration remediation
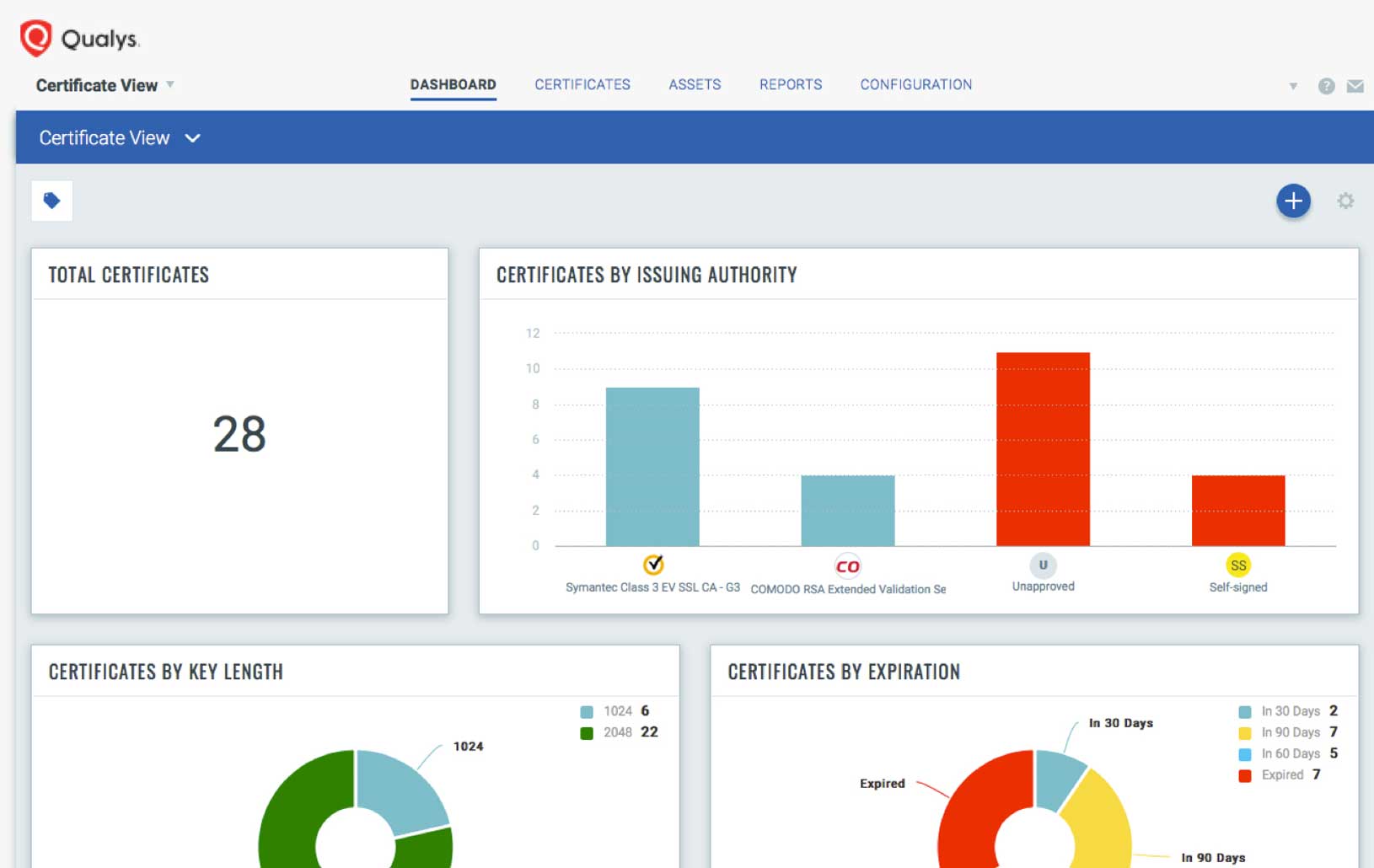
Customizable dashboards with highly configurable widgets help you see your certificate status, grade information and vulnerability data in a consolidated way. You can drill down to specific data, aggregate it into custom reports and create custom widgets based on queries. This visualization and analysis yields deep insights for immediate remediation.
Includes a variety of pre-built widgets based on the most common queries in the default dashboard setup
Allows you to create customized dashboards tailored for different IT and business roles
Lets you click through and drill down to access more information about weak and non-compliant certificates, and about vulnerable configurations
Allows you to create dashboard widgets manually or from any search query
Generates reports that you can quickly and easily share with relevant team members and executives

Combine your certificate data with configuration and vulnerability information
Qualys Certificate Assessment continuously correlates certificate and configuration information with vulnerability data, so that your remediation prioritization decisions are rooted in accurate, up-to-date, applicable data, not in outdated spreadsheets or arbitrary schedules. That way, you’ll stay a step ahead of the hackers, replacing certificates and fixing underlying TLS vulnerabilities before bad guys exploit them.
Leverages the comprehensive certificate and instance discovery of Qualys Certificate Inventory and the Six Sigma (99.9996%) vulnerability detection accuracy of Qualys Vulnerability Management
Connects the dots and flags at-risk TLS instances wherever they reside: on premises or in clouds
Lets you prioritize remediation with precision in a continuous manner
Gives a continuously accurate snapshot of all certificates and TLS vulnerabilities that exist in your environment
Allows you to assess the business impact of certificates and of the underlying configurations in your organization’s specific context

Powered by Enterprise TruRisk Platform
Single-pane-of-glass UI
See the results in one place, in seconds. With AssetView, security and compliance pros and managers get a complete and continuously updated view of all IT assets — from a single dashboard interface. Its fully customizable and lets you see the big picture, drill down into details, and generate reports for teammates and auditors. Its intuitive and easy-to-build dynamic dashboards to aggregate and correlate all of your IT security and compliance data in one place from all the various Qualys Cloud Apps. With its powerful elastic search clusters, you can now search for any asset – on-premises, endpoints and all clouds – with 2-second visibility.
Centralized & customized
Centralize discovery of host assets for multiple types of assessments. Organize host asset groups to match the structure of your business. Keep security data private with our end-to-end encryption and strong access controls. You can centrally manage users’ access to their Qualys accounts through your enterprise’s single sign-on (SSO). Qualys supports SAML 2.0-based identity service providers.
Easy deployment
Deploy from a public or private cloud — fully managed by Qualys. With Qualys, there are no servers to provision, software to install, or databases to maintain. You always have the latest Qualys features available through your browser, without setting up special client software or VPN connections.
Scalable and extensible
Scale up globally, on demand. Integrate with other systems via extensible XML-based APIs. You can use Qualys with a broad range of security and compliance systems, such as GRC, ticketing systems, SIEM, ERM, and IDS.