Qualys Product Security Advisory
Local Privilege Escalation via qagent_uninstall.sh Qualys Cloud Agents (CVE-2025-43079)
| Status: | PUBLISHED |
| CVE ID: | CVE-2025-43079 |
| Product: | Qualys Agent |
| Vendor: | Qualys Inc. |
| Discovery: | External researcher reported. |
Description
The Qualys Cloud Agent included a bundled uninstall script (qagent_uninstall.sh), that invoked multiple system commands without using absolute paths and without sanitizing the $PATH environment. If the uninstall script is executed with elevated privileges (e.g., via sudo) in an environment where $PATH has been manipulated, an attacker with root/sudo privileges could cause malicious executables to be run in place of the intended system binaries. This behavior can be leveraged for local privilege escalation and arbitrary command execution under elevated privileges.
Affected Products & Versions
- Product: Qualys Cloud Agent
- Platform: Linux
- Affected versions:
- Apple MacOS X (Intel x86 CPU 64-bit): All versions prior to 6.2.1
- Apple MacOS X (Apple M series Silicon CPU): All versions prior to 6.3.1
- AWS Bottlerocket (Intel): All versions prior to 5.0.3
- AWS Bottlerocket (ARM): All versions prior to 6.0.3
- BSD: All versions prior to 7.1
- GCP Container Optimized OS: All versions prior to 5.0.2
- Linux (x86 CPU 64-bit): All versions prior to 7.2.3
- Linux ARM: All versions prior to 6.1.1
- Linux (PowerPC CPU 64-bit): All versions prior to 3.21.1
- Linux on zSystems: All versions prior to 3.31.1
- IBM AIX: All versions prior to 6.0
- Red Hat CoreOS: All versions prior to 4.2.6
Customers are advised to upgrade to the latest version by enabling automatic updates to ensure they remain on the latest secure version.
Should additional versions of Qualys product be determined to be vulnerable, fixes will be released and QIDs will be published to drive clarity on patch availability.
If you have any uncertainty about whether your installed version is affected, treat the agent as potentially affected until you confirm via Qualys support or patch notices.
Default status in the bundle: unaffected, but the version entries above indicate affected versions. It is recommended that customers confirm the exact installed agent version on hosts.
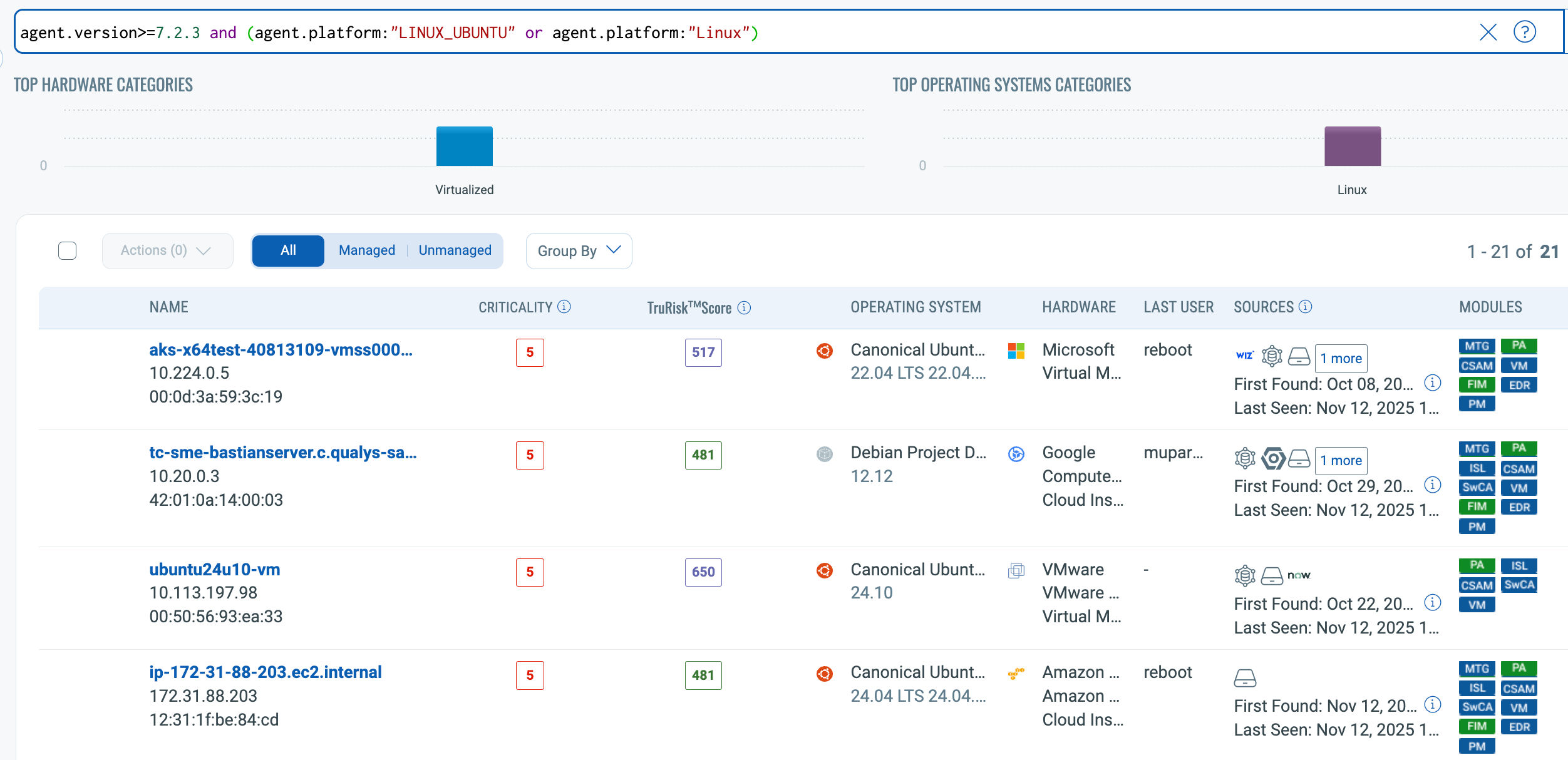
Customer can perform below operation to identify if any of their assets are running a vulnerable version of the agent.
To search by Agent Version, navigate to Inventory Tab in CSAM or GAV module and use the search filter with below query:
- agent.version<7.2.3 and (agent.platform:"LINUX_UBUNTU" or agent.platform:"Linux")
- agent.version<6.0 and agent.platform:"AIX"
- agent.version<7.1 and agent.platform:"BSD"
- agent.version<6.2.1 and agent.platform:"MACOSX"
- agent.version<6.3.1 and agent.platform:"MACOSX_M1"
Details related to End-of-Support can be found here:
https://notifications.qualys.com/notifications/2025/07/02/end-of-support-qualys-cloud-agent-versions-for-2026Impact
CVSS v3.1: CVSS:3.1/AV:L/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H
- Base score: 6.3 (MEDIUM)
- Vector highlights:
- Attack Vector: Local
- Attack Complexity: High
- Privileges Required: High (root / sudo)
- User Interaction: Required
- Confidentiality / Integrity / Availability: High
- Exploitation has only been observed through a customer-reported proof-of-concept.
Exploitation Requirements
Exploitation requires the ability to run sudo (or be root), the vulnerability is not remotely exploitable by default — it relies on local privilege and environment manipulation, but the consequences are elevated (execution under high privilege). Please read below for pre-requisites required for exploitation.
- Local access to the system (the attacker must be local).
- Ability to run sudo or root (the uninstall script requires sudo at minimum for execution or must be run as root).
- Ability to modify $PATH (temporarily in the shell session used to launch the uninstall script, or persistently via writable shell configuration files such as ~/.bashrc, ~/.zshrc).
- Execution of qagent_uninstall.sh within the compromised environment where $PATH points to attacker-controlled locations.
Technical Details
The uninstall script invoked common system utilities without absolute paths (e.g., rm, launchctl, pkginfo). When a binary is invoked by name and $PATH contains attacker-controlled directories earlier than system directories, the shell resolves to the first matching executable — which can be a malicious binary placed by an attacker. Because the uninstall script runs with elevated privileges, those malicious binaries execute with the same elevated privileges.
Core issue: Unsafe use of non-absolute command names and no sanitization/reset of $PATH before invoking system commands.
Credit
Brent Zaltsman (AfricanHipp0)
Vendor / Support
If you need confirmation about whether a particular agent build is fixed, or assistance in remediation, contact Qualys support or consult Qualys product release notes and security advisories at: https://qualys.com/.
Recommended next steps
Customers are recommended to patch to Safe Versions.
| Distribution | Affected versions | Safe Versions | QQL |
|---|---|---|---|
| Linux (x86 CPU 64-bit) | All versions prior to 7.2.3 | 7.2.3 | qualys.agent.version<=7.2.3 and (qualys.agent.platform:"LINUX_UBUNTU" or qualys.agent.platform:"Linux") |
| Linux ARM | All versions prior to 6.1.1 | 6.1.1 | qualys.agent.version<=6.1.1 and qualys.agent.platform:"LINUX_ARM" |
| IBM AIX | All versions prior to 6.0 | 6.0.0 | qualys.agent.version<=6.0 and qualys.agent.platform:"AIX" |
| BSD | All versions prior to 7.1 | 7.1.0 | qualys.agent.version<=7.1 and qualys.agent.platform:"BSD" |
| Apple MacOS X (Intel x86 CPU 64-bit) | All versions prior to 6.2.1 | 6.2.1 | qualys.agent.version<=6.2.1 and qualys.agent.platform:"MACOSX" |
| Apple MacOS X (Apple M series Silicon CPU) | All versions prior to 6.3.1 | 6.3.1 | qualys.agent.version<=6.3.1 and qualys.agent.platform:"MACOSX_M1" |
| Red Hat CoreOS | All versions prior to 4.2.6 | 4.2.6 | qualys.agent.version<=4.2.6 and qualys.agent.platform:"LINUX_COREOS" |
| GCP Container Optimized OS | All versions prior to 5.0.2 | 5.0.2 | qualys.agent.version<=5.0.2 and qualys.agent.platform:"LINUX_GCPCOS" |
| AWS Bottlerocket (Intel) | All versions prior to 5.0.3 | 5.0.3 | qualys.agent.version<=5.0.3 and qualys.agent.platform:"LINUX_AWSBR" |
| AWS Bottlerocket (ARM) | All versions prior to 6.0.3 | 6.0.3 | qualys.agent.version<=6.0.3 and qualys.agent.platform:"LINUX_AWSBR_ARM" |
| Linux (PowerPC CPU 64-bit) | All versions prior to 3.21.1 | 3.21.1 | qualys.agent.version<=3.21.1 and qualys.agent.platform:"LINUX_PPC64" |
| Linux on zSystems | All versions prior to 3.31.1 | 3.31.1 | qualys.agent.version<=3.31.1 and qualys.agent.platform:"LINUX_S390X" |