Table of Contents
- Key Takeaways`
- Introduction
- What is CI/CD Security?
- Different Types of Risks In CI/CD
- Integrating Comprehensive Scanning Across the Lifecycle
- Essential CI/CD Security Best Practices
- Aligning CI/CD Security Controls with Your Cloud Compliance Strategy
- How Qualys Enables CI/CD Security Best Practices
- Conclusion
- FAQ
CI/CD Security Best Practices: Complete Guide
Key Takeaways
- Security risks originate long before runtime — in dependencies, infrastructure-as-code templates, container images, and build artifacts.
- CI/CD security integrates automated scanning across the development lifecycle to detect vulnerabilities before software reaches production.
- Fixing vulnerabilities in production is significantly more expensive and disruptive than addressing them earlier in development.
- Effective CI/CD security balances developer productivity with production protection through workflow integration, context-driven prioritization, and progressive enforcement.
- Monitoring configuration drift is critical because secure deployments can become insecure over time.
- Modern security platforms unify application and infrastructure protection across SAST, SCA, secrets scanning, container image scanning, and runtime monitoring.
- Advanced container and cloud security capabilities are essential for protecting modern cloud-native and hybrid environments.
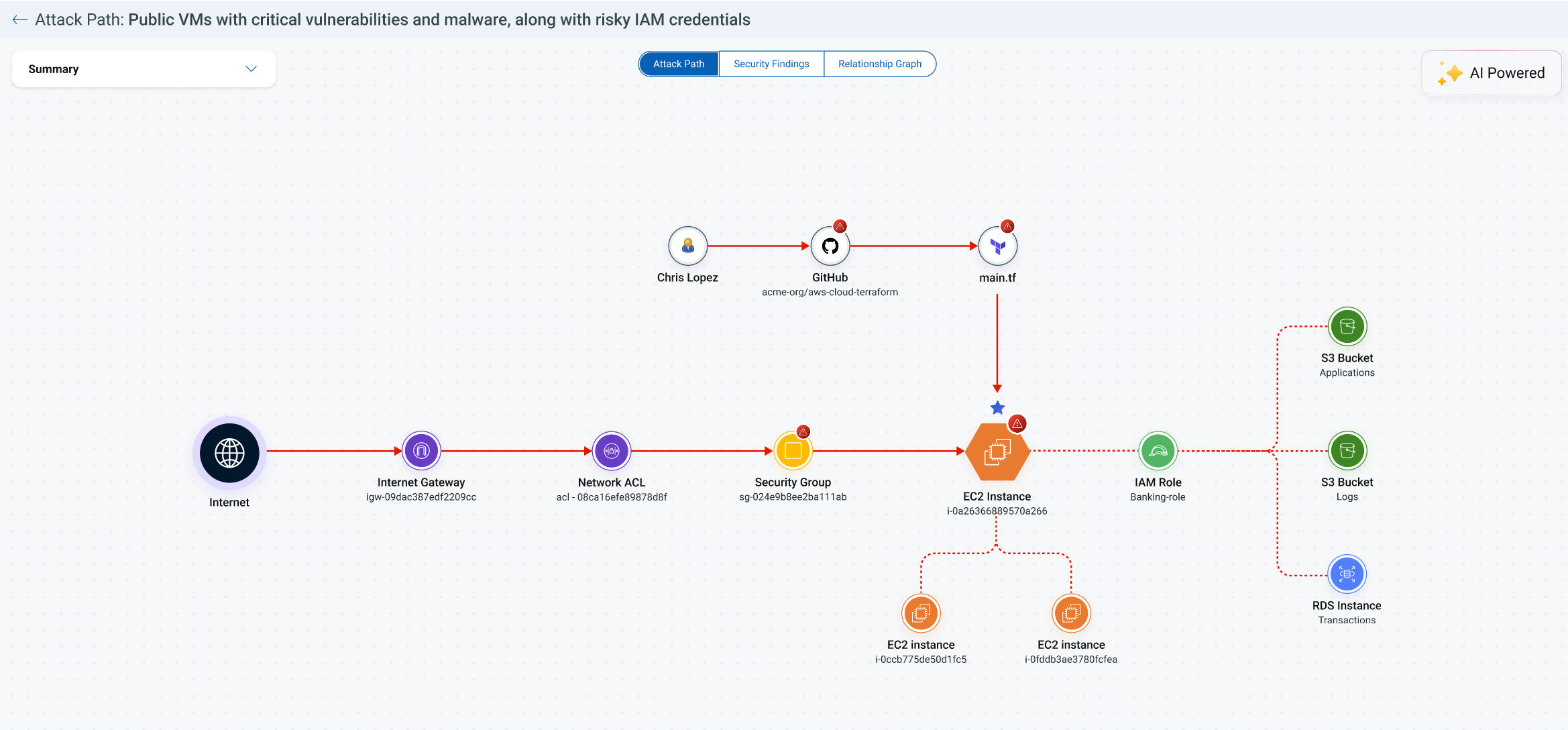
- Integrated platforms such as Qualys TotalCloud and TotalAppSec provide unified visibility and control from code to cloud.
Introduction
DevOps, DevSecOps, and CloudSecOps teams often operate against different objectives inside the CI/CD pipeline. DevOps focuses on release velocity, DevSecOps on introducing shift-left controls, and CloudSecOps on vulnerability exposure, risk, and compliance. When these priorities are not aligned, security checks appear late in the pipeline, remediation disrupts release cycles, and operational risk accumulates. The scale of the challenge is increasing. In 2025 alone, more than 40,000 new CVEs were disclosed, while risk continued to enter CI/CD pipelines through open source dependencies, container base images, infrastructure as code templates, cloud configuration
These vulnerabilities rarely originate at a single stage of delivery. Insecure dependencies, generated code flaws, and unverified components can enter during development, propagate through build artifacts, and remain unnoticed until deployment. When discovered in runtime, remediation often requires downtime, cross team coordination, and delayed releases. CI/CD security addresses this challenge by embedding continuous verification directly into the pipeline so that code, builds, and deployments are evaluated as software moves from commit to production.
What is CI/CD Security?
CI/CD security is the practice of embedding automated security checks into your build and deployment pipelines. It involves automatically checking code, configurations, and build artifacts for vulnerabilities and risks as they move through the Continuous Integration/Continuous Delivery (CI/CD) pipeline. This process ensures that security is a continuous part of software development, not a final gate.
CI/CD automates how modern software is developed and deployed, allowing changes to flow into production constantly. Without an integrated security process, risks can move just as quickly, creating significant production risk.
The CI/CD pipeline possesses broad access and automates change, which means small mistakes or compromises can scale instantly. Understanding the primary risk areas is the first step toward securing the pipeline.
Different Types of Risks in CI/CD
| Threat / Vector | What It Means | Why It Matters |
|---|---|---|
| Vulnerable Dependencies | Third-party libraries with known flaws are included in the build via Software Composition Analysis (SCA). | A single dependency can introduce exploitable risks across the entire application, creating a significant supply chain risk. |
| Insecure Code | Flaws like SQL injection or cross-site scripting are present in the source code, detected by Static Application Security Testing (SAST). | Insecure code patterns create direct entry points for attackers to exploit application logic and access sensitive data. |
| Misconfigured IaC | Terraform or CloudFormation templates contain settings that expose cloud resources to unnecessary risk. | Insecure infrastructure configurations are deployed automatically and repeatedly, creating systemic weaknesses in your cloud environment. |
| Secrets in Code | API keys, passwords, or tokens are committed to the source control repository instead of a secure vault. | Once exposed, these credentials can be used to gain unauthorized access to sensitive systems and data. |
| Compromised Build Artifacts | Container images or binaries have insecure dependencies, OS-level vulnerabilities, or embedded malware. | The pipeline distributes the compromised artifact to every environment it deploys to, scaling the threat instantly. |
| Runtime Drift | Secure deployments become insecure over time due to manual configuration changes or unmanaged updates. | Security is not a one-time event. Drift can silently reopen known risks and introduce new ones without visibility. |
| Insecure APIs | Applications expose APIs that lack proper authentication, authorization, or schema validation. | Modern applications rely heavily on APIs. Weak API security controls can allow attackers to bypass authentication, access sensitive data, or abuse application logic. |
| AI-Generated Code and Model Dependencies | Code produced by AI assistants or external AI services may introduce insecure patterns, unsafe dependencies, or unverified third-party components. | AI-generated code can accelerate development but may introduce vulnerabilities, insecure libraries, or logic flaws that propagate quickly through CI/CD pipelines if not validated. |
Integrating Comprehensive Scanning Across the Lifecycle
A robust strategy integrates multiple scanning types to provide layered defense that spans the entire software development lifecycle from code, build, registry, cloud, and runtime:
- Software Composition Analysis (SCA): Scans open-source libraries for known vulnerabilities and license risks. SCA should be a standard part of your build process to secure the software supply chain.
- Secrets Scanning: Searches for hard-coded credentials like API keys and passwords in your code, configurations, and build artifacts. This should run as a pre-commit hook and a pipeline step.
- Container & VM Image Scanning: Analyzes container & VM images for vulnerabilities and risks in the OS and application layers. Scan images in your CI pipeline and in the registry before deployment.
- Static Application Security Testing (SAST): Analyzes source code for insecure patterns before it is compiled. Integrate SAST to run on every commit or pull request for immediate developer feedback.
- Dynamic Application Security Testing (DAST) and API Security Testing: While static analysis identifies code issues, dynamic testing evaluates running applications for vulnerabilities such as authentication flaws, injection attacks, insecure session handling, and API exposure risks. Integrating DAST and API testing into staging environments helps detect issues that only appear during application execution.
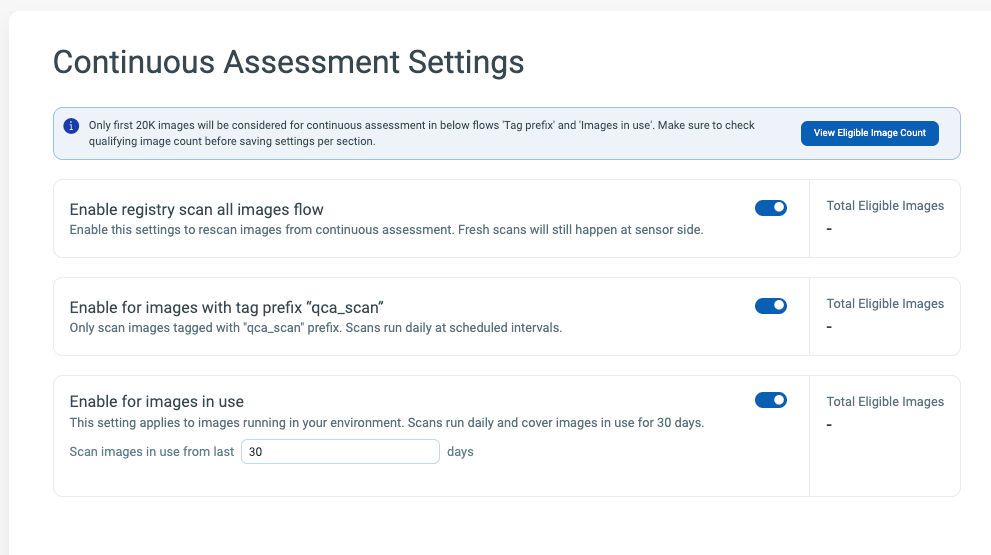
- Continuous Assessment of Image Registries: New images are continuously pushed to registries, but like books in a library, are not always checked out and running in production. However, it is important to continuously assess these images against new vulnerabilities & threat intel as they can be deployed at any time.
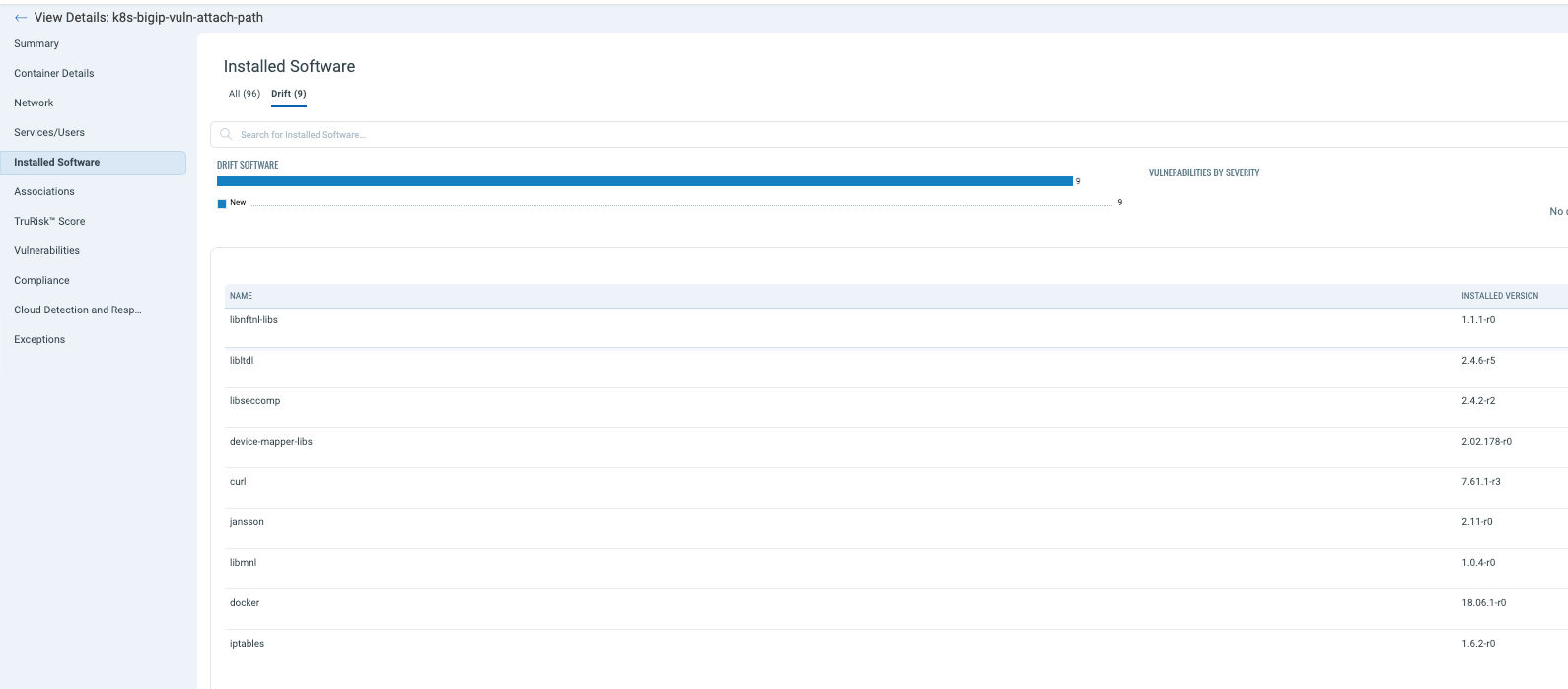
- Runtime Workload Protection (CWP) & Container Security: Continuously scan running containers, VMs and serverless to address drift in production environments. While baseline policies (for e.g. not scanned by your tool, cannot run) may exist, adding visibility in production for example via eBPF or cloud agents protects against residual risk that could come from bypassing CI/CD pipelines. In addition, it helps to monitor drift that could come from installing new software that was not attested and validated pre-deployment.
- Cloud Security Posture Management (CSPM): CSPM provides a means to continuously assess your infrastructure for misconfigurations & compliance violations. CSPM tooling also helps protect against drifts – i.e. mismatches between what is configured in production and what is defined as a secure configuration in IaC.
- AI-Generated Code and Model Dependency Validation: As organizations increasingly adopt AI-assisted development and AI services, CI/CD pipelines should also validate AI-generated code, external model dependencies, and third-party inference APIs. This helps prevent insecure generated code patterns or unverified components from entering production environments. Static Application Security Testing (SAST): Analyzes source code for insecure patterns before it is compiled. Integrate SAST to run on every commit or pull request for immediate developer feedback.
- Dynamic Application Security Testing (DAST) and API Security Testing: While static analysis identifies code issues, dynamic testing evaluates running applications for vulnerabilities such as authentication flaws, injection attacks, insecure session handling, and API exposure risks. Integrating DAST and API testing into staging environments helps detect issues that only appear during application execution.
- Continuous Assessment of Image Registries: New images are continuously pushed to registries, but like books in a library, are not always checked out and running in production. However, it is important to continuously assess these images against new vulnerabilities & threat intel as they can be deployed at any time.
- Runtime Workload Protection (CWP) & Container Security: Continuously scan running containers, VMs and serverless to address drift in production environments. While baseline policies (for e.g. not scanned by your tool, cannot run) may exist, adding visibility in production for example via eBPF or cloud agents protects against residual risk that could come from bypassing CI/CD pipelines. In addition, it helps to monitor drift that could come from installing new software that was not attested and validated pre-deployment.
- Cloud Security Posture Management (CSPM): CSPM provides a means to continuously assess your infrastructure for misconfigurations & compliance violations. CSPM tooling also helps protect against drifts – i.e. mismatches between what is configured in production and what is defined as a secure configuration in IaC.
- AI-Generated Code and Model Dependency Validation: As organizations increasingly adopt AI-assisted development and AI services, CI/CD pipelines should also validate AI-generated code, external model dependencies, and third-party inference APIs. This helps prevent insecure generated code patterns or unverified components from entering production environments.
Essential CI/CD Security Best Practices
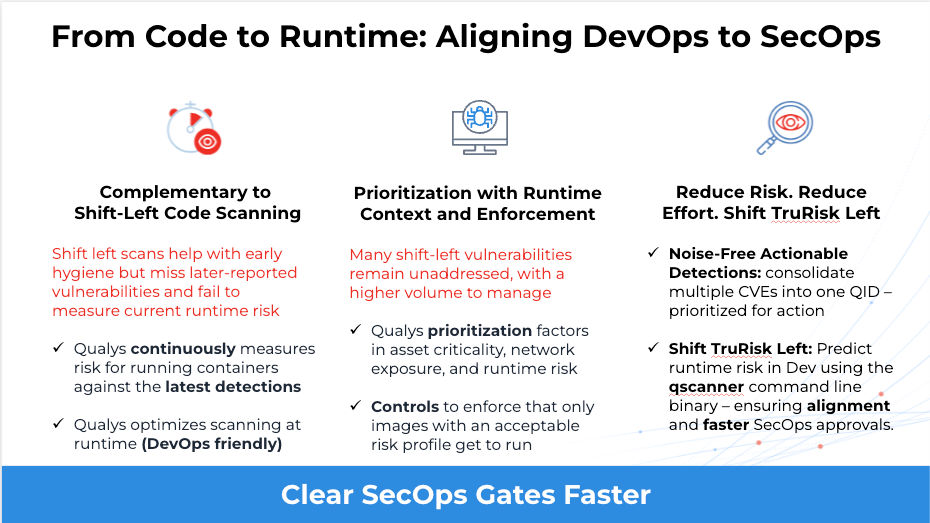
Modern CI/CD pipelines move code to production faster than ever before. Security can no longer rely on periodic scanning or reactive alerting. Instead, organizations need security practices that integrate directly into development workflows while prioritizing the risks that actually matter.
The following best practices help organizations build DevSecOps harmony — where security improves developer velocity instead of slowing it down.
1. Context-Based and Threat-Informed Risk Prioritization
Not all vulnerabilities are equally dangerous. Traditional security approaches often overwhelm teams by flagging every possible issue, regardless of real-world exploitability or operational impact.
Modern CI/CD security requires context-driven risk prioritization that evaluates vulnerabilities based on factors such as:
- Business criticality of the affected asset
- Internet exposure or attack surface
- Presence of active exploits or threat intelligence
- Runtime usage of vulnerable components
- Attack path potential across infrastructure, identities, and workloads
By incorporating this context directly into CI/CD workflows, developers receive actionable remediation guidance instead of long lists of low-impact findings. The goal is simple: fix what matters, not everything.
This approach reduces alert fatigue while ensuring security teams focus remediation efforts on vulnerabilities that present real business risk.
2. Continuous Asset Tracing and Ownership Mapping
One of the biggest blockers to vulnerability remediation is uncertainty around ownership.
Security teams frequently detect issues in containers, dependencies, or infrastructure but lack visibility into which team or service owner is responsible for fixing them.
Effective CI/CD security requires continuous traceability between development artifacts and production workloads, including:
- Source code repositories and commits
- Build artifacts and dependencies
- Container/VM images (including AMIs for e.g. in AWS) and layers
- Container registries and deployed workloads
- Responsible teams or service owners
With this traceability in place, vulnerabilities discovered at any stage of the lifecycle — including runtime — can be traced back to the originating code, image, or development team responsible for remediation.
This dramatically reduces mean time to remediation and eliminates manual investigation.
3. Meet Developers Where They Work
Security tooling is most effective when it integrates directly into the tools developers already use.
Instead of requiring developers to learn new security platforms or dashboards, security insights should surface directly within existing workflows such as:
- Git repositories and pull requests
- CI/CD pipelines and build tools
- IDE environments used during development
- Ticketing systems such as Jira or ServiceNow
This approach ensures developers encounter security guidance at the moment decisions are made, allowing vulnerabilities to be addressed during development rather than after deployment.
When security feedback is embedded directly in developer workflows, organizations can implement shift-left security without slowing development velocity.
4. Secure the Software Supply Chain
Modern applications depend heavily on open-source libraries, container base images, build pipelines, and third-party services. This creates a complex software supply chain that must be secured across the entire CI/CD lifecycle.
Key supply chain protections include:
- Software Bills of Materials (SBOMs) to track dependencies
- Software attestations verifying build integrity
- Image signing and verification to prevent artifact tampering
- SLSA (Supply-chain Levels for Software Artifacts) to strengthen pipeline security
- Validation of external dependencies and build artifacts
These practices help ensure that only verified, trusted software components move through the CI/CD pipeline and into production environments.
5. Continuous Registry and Artifact Assessment
Security scanning should not stop once a container image or build artifact is created.
New vulnerabilities and exploits are discovered every day, meaning previously safe artifacts can quickly become high risk.
Organizations should continuously reassess:
- Container registries
- Artifact repositories
- Build outputs and software dependencies
Continuous reassessment ensures that newly disclosed vulnerabilities are immediately detected — even in images or artifacts that were built weeks or months earlier.
This approach helps organizations maintain an up-to-date understanding of risk across their container and software environments.
6. Pre-Deployment Guardrails and Baseline Policies
Security policies are most effective when they act as guardrails rather than blockers.
Instead of attempting to enforce perfect security from the beginning, organizations should define baseline security policies that prevent clearly unacceptable risks from reaching production environments.
Examples include:
- Blocking deployment of workloads with actively exploited vulnerabilities
- Preventing unsigned or unverified images from running in production
- Requiring security scans before artifacts can be deployed
- Enforcing minimum security standards for container images or dependencies
These guardrails establish a minimum security baseline, while allowing development teams to continue delivering quickly.
Over time, policies can be refined and strengthened as organizations mature their DevSecOps practices.
7. Runtime Monitoring and Drift Detection
Even with strong CI/CD security controls, production environments can change over time.
Containers, infrastructure configurations, or dependencies may drift from their original state due to updates, manual changes, or emerging vulnerabilities.
Runtime monitoring helps ensure security remains intact after deployment by detecting:
- Configuration drift from approved images or infrastructure-as-code templates
- Suspicious runtime behavior or exploitation attempts
- Unauthorized software installation or dependency changes
- Lateral movement or abnormal cloud activity
By correlating runtime telemetry with earlier development and build stages, organizations can create a closed-loop security model where runtime insights continuously improve CI/CD security posture.
The Goal: DevSecOps Harmony
When implemented together, these practices transform CI/CD security from a reactive process into a continuous feedback loop between development, security, and operations.
Instead of slowing delivery, security becomes an integrated system of guardrails, context, and automation — enabling organizations to move from fragmented security checks to a unified code-to-cloud security model that continuously reduces risk without slowing innovation.
Aligning CI/CD Security Controls with Your Cloud Compliance Strategy
Many organizations must prove their security posture to auditors and regulators. Automated compliance checks map your security controls to frameworks like SOC 2, ISO 27001, and PCI DSS. By embedding these checks into the pipeline and runtime, you can enforce policy continuously and block non-compliant changes from reaching production.
Optimal solutions support centralized control coverage mapped to major frameworks, custom control creation, continuous drift detection, and unified visibility for real-time audit readiness across hybrid environments.
This process generates an immutable audit trail, providing evidence of who triggered deployments, what scans ran, and how issues were remediated.
| Security Control | SOC 2 | ISO 27001 | NIST 800-53 | CIS Controls | PCI DSS |
|---|---|---|---|---|---|
| IaC Security Scanning | CC7.2 | A.14.2.1 | SA-11 | 18.3 | 6.3.1 |
| Secrets Scanning | CC6.1 | A.9.4.1 | IA-5 | 3.3 | 8.2.1 |
| Container Image Scanning | CC7.2 | A.12.6.1 | RA-5 | 7.3 | 6.2 |
| SAST/SCA Scanning | CC7.2 | A.8.16 | SA-4(6) | 2.4 | 6.3.2 |
| Pipeline Access Control | CC6.1 | A.9.2.1 | AC-2, AC-3 | 6.1 | 7.1 |
| Image Signing/Provenance | CC7.2 | A.8.16 | SA-10 | 2.5 | 6.3.2 |
| Admission Policies | CC7.2 | A.14.2.9 | CM-7 | 4.1 | 2.2 |
| Runtime Drift Detection / File Integrity Monitoring | CC7.2 | A.12.7.1 | SI-7 | 5.1 | 11.5 |
How Qualys Enables CI/CD Security Best Practices
Implementing CI/CD security across the software lifecycle requires unified visibility across application code, software dependencies, container artifacts, and cloud runtime environments.
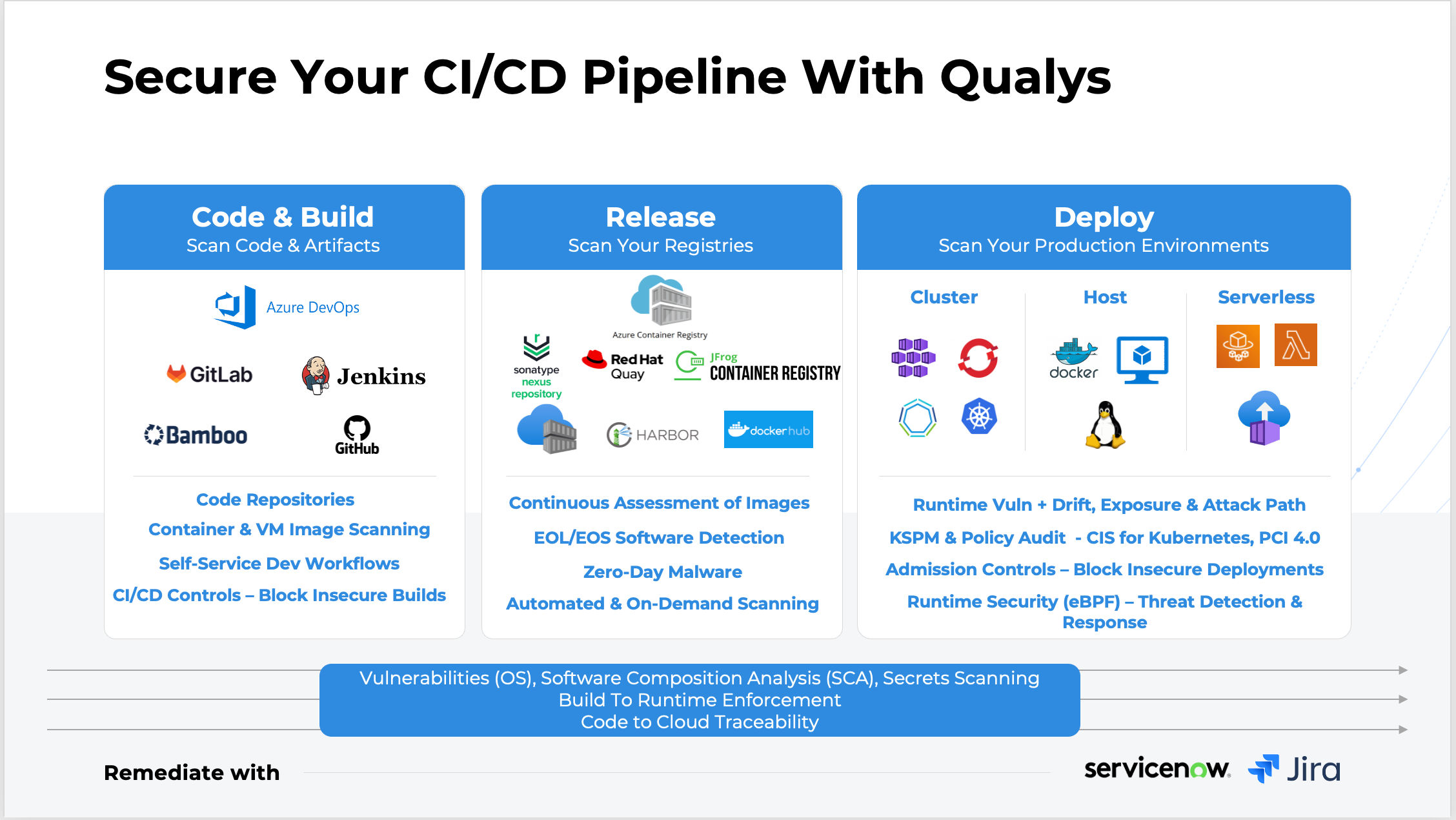
Qualys enables this through an integrated platform combining Qualys TotalCloud, TotalAppSec, QScanner, and TotalAI, delivering security from code to cloud to runtime.
Key capabilities include:
- Identify infrastructure misconfigurations before deployment by scanning Infrastructure-as-Code templates such as Terraform, Kubernetes manifests, and cloud configuration files, preventing insecure infrastructure from being automatically provisioned.
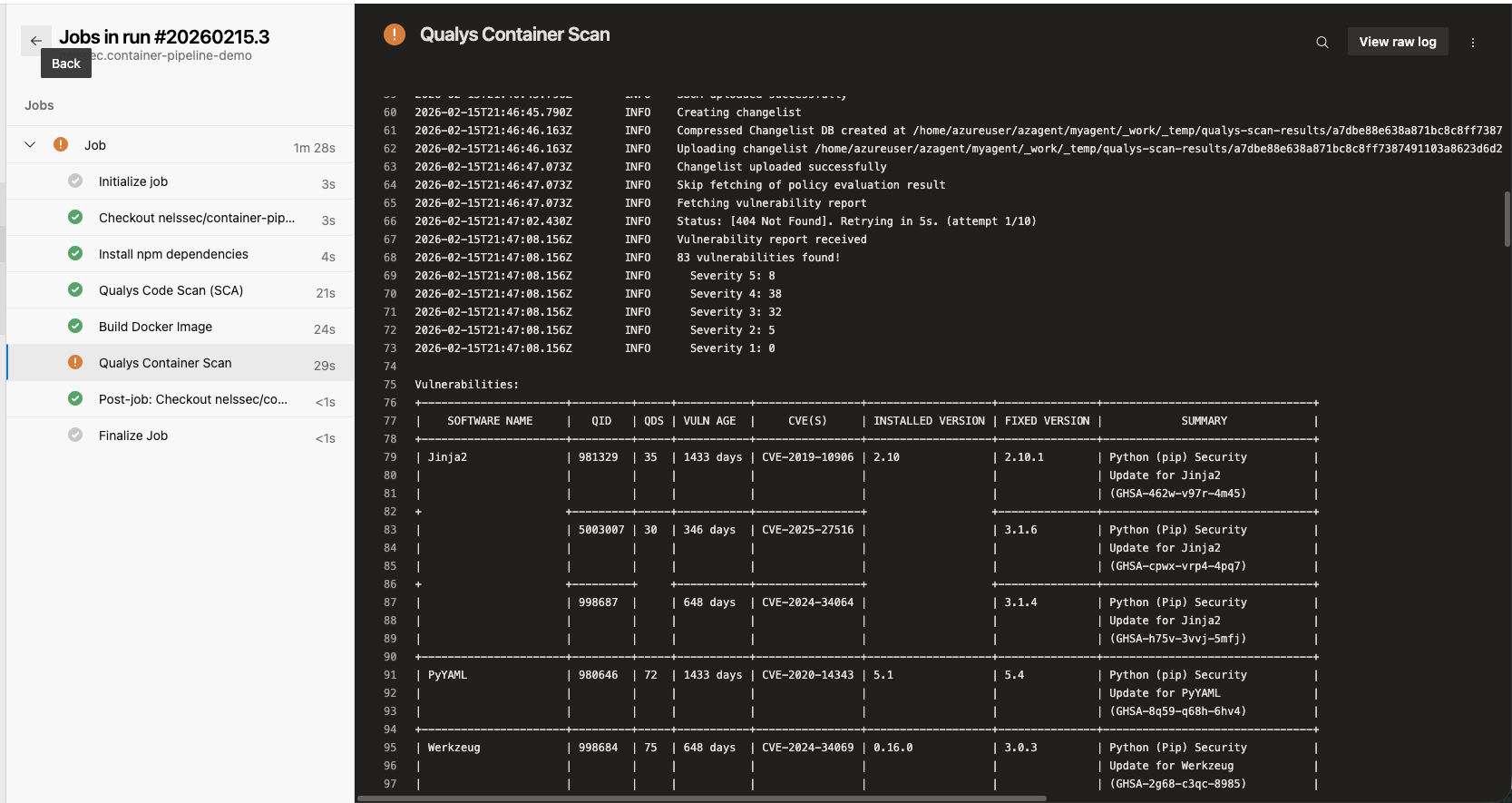
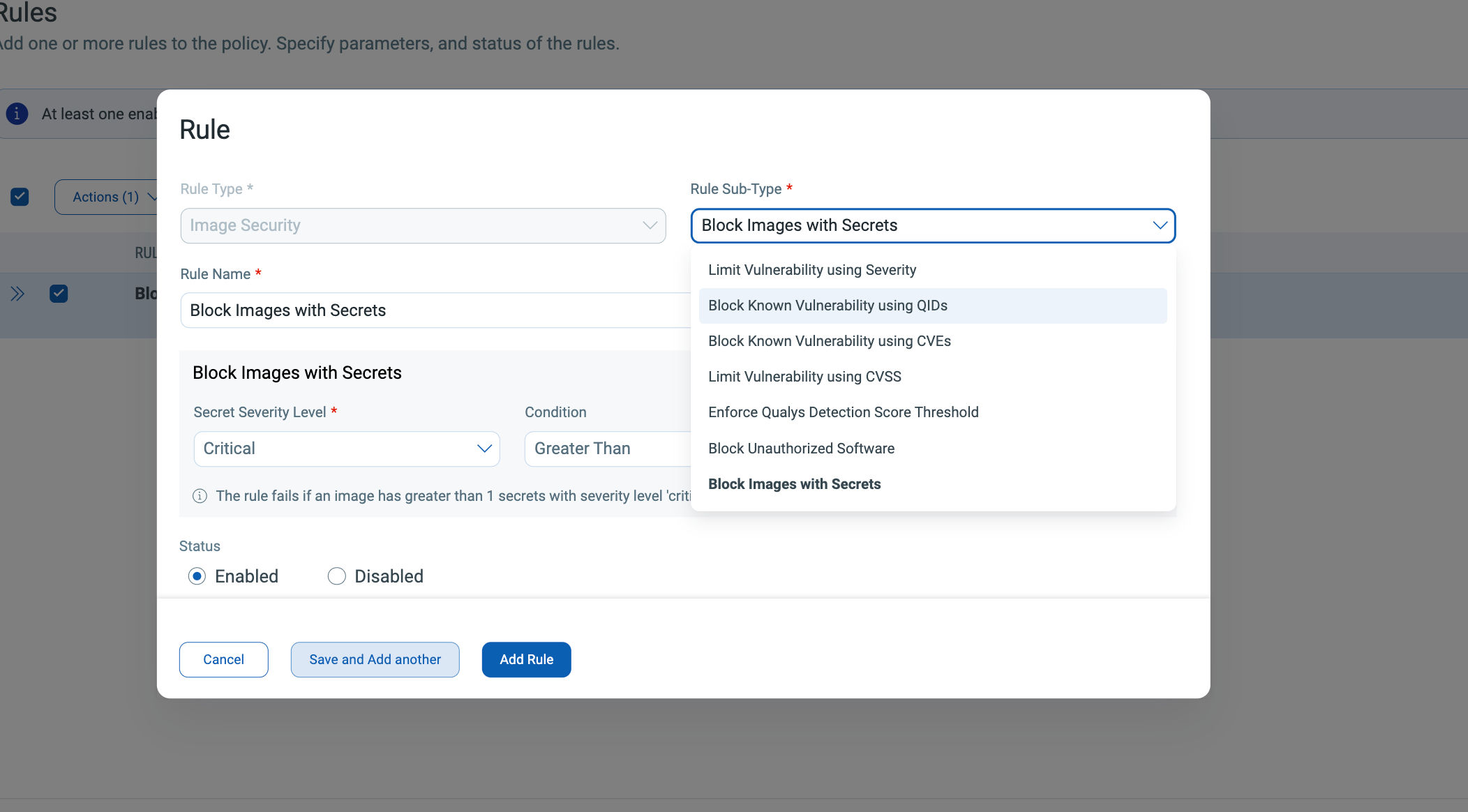
- Prevent vulnerable container images from reaching production through comprehensive container, VM image, and AMI scanning across both CI pipelines and container registries with the ability to establish baseline policies and pre-deployment guardrails with Qualys Admission Controller
- Continuously reassess container registries and software artifacts so newly disclosed vulnerabilities are detected immediately — even in images that were built weeks or months earlier — without requiring repeated full scans.
- Detect application and API vulnerabilities early in development using DAST, SCA, and secrets scanning integrated directly into CI/CD pipelines through Qualys TotalAppSec and QScanner, helping developers remediate issues before code reaches production.
- Correlate vulnerabilities with runtime exposure and cloud context to prioritize remediation based on real-world risk instead of static severity scores alone.
- Monitor runtime containers and cloud workloads for drift, exploitation attempts, and abnormal behavior, ensuring security controls remain effective even after software is deployed.
- Continuously evaluate cloud environments for misconfigurations and compliance risks through integrated Cloud Security Posture Management (CSPM) across multi-cloud environments.
- Secure emerging AI-driven development and AI workloads by discovering AI models, analyzing dependencies, and monitoring AI services and APIs with Qualys TotalAI.
Together, these capabilities help organizations embed security across CI/CD pipelines while maintaining continuous visibility across the entire code-to-cloud lifecycle.
Conclusion
CI/CD security is evolving from shift-left scanning toward continuous risk management across the entire software delivery lifecycle. Modern CI/CD pipelines require real-time security assessment, AI-driven vulnerability prioritization, and automated remediation that can operate at the same speed as development. By analyzing exploitability, asset criticality, and real-world attack patterns, AI-powered vulnerability management allows security teams to focus on the small set of vulnerabilities that represent genuine operational risk, enabling organizations to secure CI/CD pipelines without slowing release velocity.
As cloud-native development accelerates, DevSecOps is becoming an operational discipline embedded directly into the CI/CD workflow. Security, development, and operations increasingly rely on continuous vulnerability assessment, container security, and runtime risk monitoring to guide release decisions from code to production. The result is a modern CI/CD security model where vulnerabilities are continuously identified, prioritized, and remediated across pipelines, containers, and cloud workloads while software delivery continues at speed.
Frequently Asked Questions (FAQs)
What is CI/CD security?
CI/CD security is the practice of embedding automated security checks into the continuous integration and continuous delivery pipeline. It ensures that application code, dependencies, infrastructure configurations, and build artifacts are scanned for vulnerabilities before software is deployed to production.
Why is CI/CD security important?
CI/CD pipelines automate software delivery and often have access to critical infrastructure, repositories, and deployment systems. Without integrated security controls, vulnerabilities introduced during development can quickly propagate into production environments. CI/CD security helps detect risks early and prevent insecure code or artifacts from being deployed.
What security checks should run in a CI/CD pipeline?
A secure CI/CD pipeline typically includes multiple security checks across the software lifecycle, including:
- Static Application Security Testing (SAST)
- Software Composition Analysis (SCA)
- Secrets scanning
- Infrastructure-as-Code (IaC) scanning
- Container and VM image scanning
- API and application testing (DAST)
- Runtime workload monitoring
These controls help identify vulnerabilities at different stages of development and deployment.
How do you secure container images in CI/CD pipelines?
Container images can be secured by scanning them during the build process and continuously reassessing container registries for newly disclosed vulnerabilities. Security teams can also enforce policies that prevent images with high-risk vulnerabilities from being deployed into production environments.
What is shift-left security in CI/CD?
Shift-left security is the practice of moving security testing earlier in the software development lifecycle. Instead of detecting vulnerabilities after deployment, shift-left security integrates scanning directly into development workflows such as code commits, pull requests, and CI builds so developers can fix issues earlier.
What is the difference between SAST, SCA, and DAST?
SAST analyzes source code to detect insecure coding patterns before applications are compiled.
SCA scans open-source libraries and dependencies for known vulnerabilities.
DAST tests running applications for vulnerabilities that only appear during execution, such as authentication issues or injection attacks.
Together, these approaches provide comprehensive application security coverage.
How does CI/CD security help protect the software supply chain?
CI/CD security protects the software supply chain by verifying dependencies, validating build artifacts, and continuously scanning container images and software components. This helps prevent vulnerable or malicious components from entering production environments.
What are the biggest risks in CI/CD pipelines?
Common CI/CD pipeline risks include vulnerable dependencies, insecure code, exposed secrets, compromised build artifacts, misconfigured infrastructure-as-code templates, and runtime configuration drift. Attackers often target CI/CD pipelines because they provide direct access to software builds and deployment environments.
How does CI/CD security support compliance?
CI/CD security helps organizations enforce security controls required by compliance frameworks such as SOC 2, ISO 27001, NIST, and PCI DSS. Automated security checks in the pipeline create an auditable record of code scanning, artifact validation, and deployment approvals, which simplifies compliance reporting.
What tools help secure CI/CD pipelines?
CI/CD pipelines are typically secured using a combination of application security testing tools, container security platforms, cloud security posture management solutions, and runtime workload monitoring technologies. These tools provide visibility and enforcement across development pipelines, container registries, and production environments.